What Are Audit Logs?
An audit log (also known as an audit trail) is a chronological, secure record, or set of records, that provide evidence that activities or a sequence of activities have affected an operation, procedure, or event. In other words, when any change is made to a system’s behavior, that change is documented in an audit log.
In it’s simplest form, an audit log could be made by pen and paper. Using a timecard to punch in and out of work is an example of a very basic audit log. It documents that something has happened and makes a record. But in the digital world, digital records are made whenever a change is made, and those records are kept secure and””ideally””immune from tampering. Furthermore, in modern digital record keeping, audit logs are impossible to avoid. When a change is made, a record of that change takes place.
What Are Audit Logs Used For?
Developers use audit logs to keep track of changes that are made to their systems, to figure out what makes a certain system break and figure out how to repair it. If something has been deleted, an audit log is created and the developer can find out when and (hopefully) why the change was made. With this knowledge the developer can track down the person or process responsible for the change, and, if necessary, fix the problem.
Audit logs are also essential for compliance. When legal concerns are at stake””for example, if you’re dealing with medical records, or financial records, audit logs are crucial to maintaining the security of your information. As the name suggests, audit logs are there in case you need to audit a system””to scrutinize it and make sure that everything that happened when changes were made was necessary, legal, and in accordance with best practices.
There are, on the other hand, times when audit logs are not necessary (or less necessary). Obviously, not every change to every record in a system can be logged without creating enormous backup files. When an audit management software is in its infancy and developers are scrambling to get it built, they may not rely on audit logs because of the added time and data sink. But eventually, audit logging will eventually be necessary.
Why Audit Logging?
One major reason for audit logging is accountability. When an audit log is created, it generally keeps track of the user who made the change, the change they made, the security level they had, and the reason for the change. This way, when an audit is made, the party in question can be identified and a breadcrumb trail can lead the auditor (or developer) through the entire process, identifying why, what and when a change was made.
Similarly, audit logs help developers to reconstruct events and identify the situations in which they occurred and how they can be replayed to illustrate what happened and why. Breakdowns in the system can be recreated and examined, and data””that may have been lost, corrupted, or deleted””can be restored.
Audit logs can be used for security and forensics. Because audit logs are taken when a specific user or process makes a change, if there was an error””intentional or not””it can be tracked down to a specific individual who can be questioned and investigated. The information can be used to see if the user had been hacked (at which point a much wider audit would follow to investigate further damage) or if the user had acted alone. Logs can show who and when specific files were copied, printed, or deleted.
Audit Logging for Compliance and Security
Without audit logging, any action can be taken in a system and go completely unnoticed. This is a significant risk when trying to protect your system and recover compromised data. Audit logs are indeed valuable for detecting and analyzing system issues, but they are also the very basics of a security system.
Security compliance programs reflect industry best practices and focus on high risk, and audit logging is a very essential part of that.
An audit log can vary from application to application, but some of the most common factors of an audit log are:
- Timestamp
- Event, status, and error codes
- Service/command/application name
- User or system account associated with the event
- Device used
- Operating system used
How Data Rooms Work With Audit Logging
A data room, or a space used for housing data, is usually a secure area. They can be virtual rooms, physical spaces, or data centers. They can be used for a variety of purposes, including data storage, document exchange, file sharing, financial transactions, legal transactions, and more.
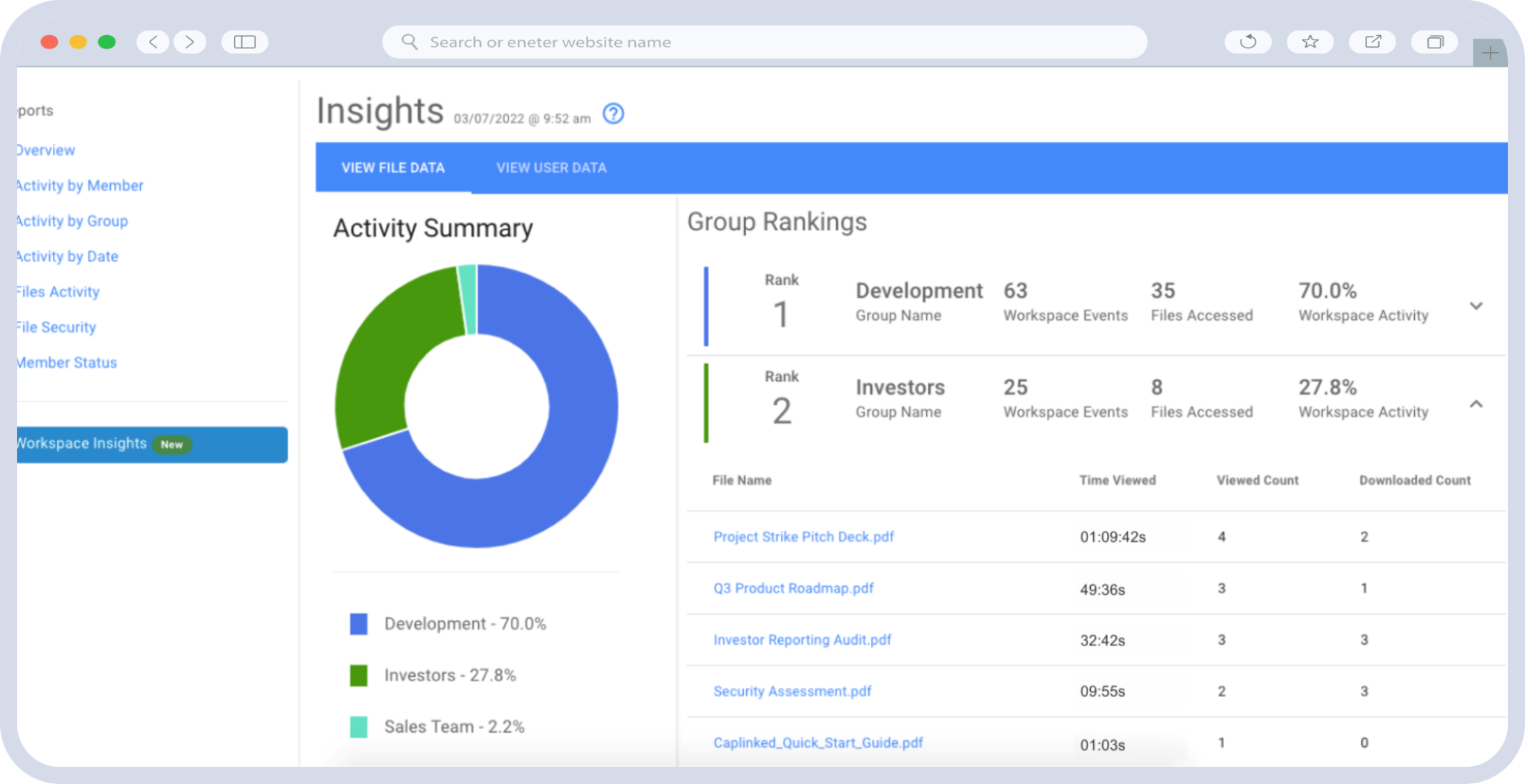
Audit logs work in data rooms as an action-based record of all user activity. The audit log, or log trail, is used by room administrators to track changes, transactions, deletions, and all other intrusions into the data.