Updated Feb 11, 2024
Protecting sensitive data remains an enormous challenge in virtually every industry, and especially so for industries that are governed by strict privacy regulations like healthcare. Data security is paramount — losing control of patient or facility records isn’t merely an inconvenience — serious legal and financial consequences are at stake here for non-compliance.
Knowing how to manage electronic documents effectively and securely, users in the healthcare arena also need to be acutely aware of any potential flaws in the system and how to avoid these pitfalls. To ensure compliance and mitigate legal and financial risks, implementing robust and reliable HIPAA-compliant document management software becomes essential, enabling healthcare professionals to effectively and securely manage electronic documents while avoiding potential system vulnerabilities.
Table of Contents
ToggleHIPAA
The medical field has a series of standards for dealing with healthcare information, namely the Health Insurance Portability and Accountability Act of 1996 (commonly referred to as HIPAA). HIPAA, a Congressional Act, deals with (among other issues related to medical data and patient privacy) how this information is to be maintained by the healthcare and insurance industries.
In addition to being mandated by law, acts such as HIPAA are useful for helping healthcare facilities stay compliant, giving them an incentive to proactively maintain health information.
This data, including electronic health records (EHR), is a vital part of any healthcare facility’s IT structure. Methods and systems for protecting this data require robust security standards to be enacted in order to protect it from assaults, whether internal or external. Any flaws in the system can result in hacks or data breach, both of which are expensive in financial areas and in the overall reputation of your organization.
Where (and How) Data Can Be Compromised
Personal healthcare information is like gold on the black market, right up there with financial and credit data. Sophisticated security surrounding medical data is important for preventing healthcare records from being compromised. Data breaches cost providers billions of dollars every year, and unfortunately, this figure tends to climb annually. Many scenarios of how this data can be compromised include:
Theft of Hard Copy Records
Despite our reliance on all things digital, there are some instances where medical records are still hardcopy-based. Simply walking off with a folder or copying any healthcare or patient record is one way that information is stolen. Fortunately, this way of storing data is quickly being phased out.
Unauthorized Access to a Cloud-Based System
Being able to control who is coming and going in your digital workspace is key. If you are using a system that doesn’t give specific users assigned roles, doesn’t have the ability to log and track user activity, or one that allows users to copy or forward information to a non-secure server, there is plenty of room for data theft.
Stolen Devices or Copied Data
Healthcare or patient information stored on a laptop or tablet is certainly not immune to theft. Devices can be stolen or data can easily be copied to a USB flash drive. Not a particularly sophisticated method, but one that is preventable.
Mistakes or Carelessness
Of course, some mistakes are unavoidable, but a little knowledge can go a long way. Things, like not securing login credentials for a server or improperly expunging data from an obsolete device, should be avoided.
A Solution: Virtual Data Rooms
One of the most sophisticated solutions to securely store and share healthcare information is using a secure virtual data room (commonly referred to as VDR). What is a data room? It is a highly secure server that allows companies to distribute data in an online workspace.
When it comes to sharing confidential digital data, a VDR is mandatory. Having the ability to encrypt data, control access, positively authenticate users and record activity are all tools that add up to healthcare information security. Knowing what to look for in a virtual data room provider is also key. The features you should consider in a VDR include the following:
- Security and reliability: Needless to say, these features speak for themselves. There are many facets of security to look for, including both internal and external access to the data, document control and levels of encryption that are offered.
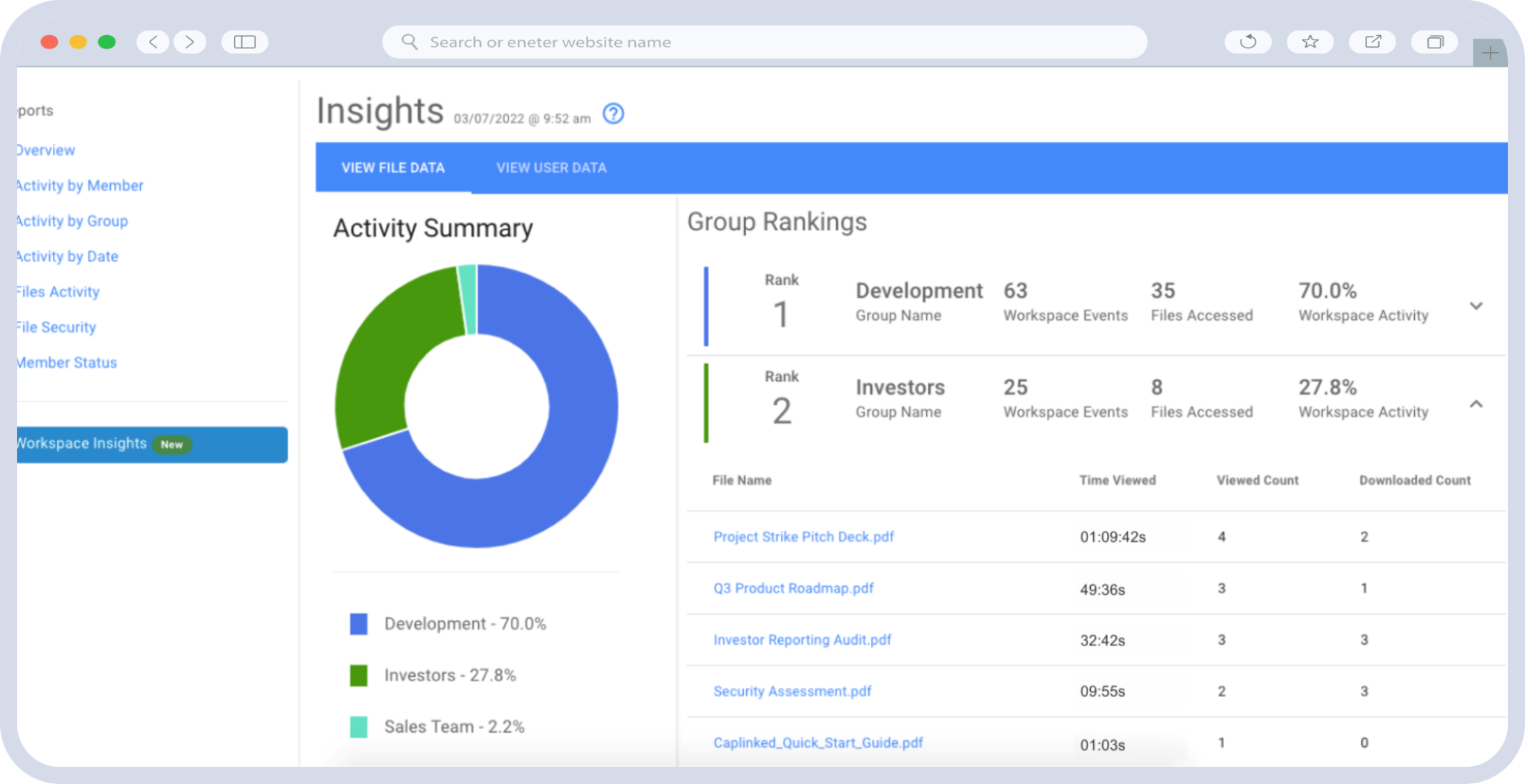
- Interface: Being able to access all areas of the virtual data room, monitor the activity logs and add and revoke privileges are important features to consider.
- Support: Knowing what level of support you will receive and having a service level agreement (SLA) in place will help clarify exactly how much and how often this level of support is supplied.
In Conclusion
Having virtual data protection of your organization’s medical and patient care records is something that must be given high priority and proactively maintained. Knowing how your healthcare data security works as well as monitoring the system is paramount for keeping your sensitive data safe, both inside and outside of your organization.
In addition, when it comes to selecting a virtual data room organization to partner with, it’s critical that you do your homework and make an educated decision about that provider. You need to select a trusted provider like Caplinked that not only has the tools that will allow you to easily and securely manage and share your data, but who also has a reputation for uptime, security and 24/7 customer service. Learn more about how we can transform your healthcare document management by beginning a free trial today.
Chris Capelle is a technology expert, writer and instructor. For over 25 years, he has worked in the publishing, advertising and consumer products industries.