Cybersecurity breaches have become all too common. Incidents of malware, ransomware, trojans and phishing have all spiked at unprecedented rates, with attacks becoming more sophisticated, more coordinated and, when they strike, more devastating to companies than ever before.
The security of your most important digital documents should be the last bastion in any organization’s cybersecurity defense plans — a virtual “safe room,” if you will, that is unreachable by bots, viruses or human bad actors intent on using your company’s data for their own criminal ends.
What’s the Real Risk?
In today’s digital age, no business is an island. Your organization depends on a deep network of trust that extends far beyond your own employees to your business partners, suppliers, clients and the organizations they in turn are associated with.
If you do a quick search of cyberattack news reports, you’ll find pages and pages of results, and, because they have become so commonplace, the majority of breaches don’t even make the news. The top ten list from 2020 is massive, representing breaches of millions of sensitive files and representing millions in losses for the companies involved.
The top ten security breaches of 2020 included the following.
- Toll Group: attacked with unrelated ransomware twice within three months, forcing the company to shut down systems, including customer-facing applications
- Marriott International: suffered a second major data breach in two years, exposing the confidential information of 5.2 million guests
- Magellan: attacked by ransomware, jeopardizing the data of 365,000 health care patients
- Twitter: had some of its highest-profile accounts breached through phone-based phishing attacks targeting Twitter employees
- Garmin: was the victim of an unspecified cyberattack, with some media outlets reporting that the company paid as much as $10 million to ransomware attackers
- Software AG: had confidential files leaked online after it declined to pay a $20 million ransomware demand
- Vastaamo Psychotherapy Centre: after a data breach of its patient records, over 25,000 patients were extorted by the hackers threatening to make their records publicly available
- FireEye and SolarWinds: after the security vendor FireEye had been breached, a multitude of companies and government department networks were accessed by hackers
In many ways, the major attacks of 2020 were just a warm-up for 2021. In the past 18 months, cyberattacks have increased by 600 percent. Ransomware has particularly become so bad that the Biden administration made tackling the problem a national security priority earlier this year.
The Most Recent Major Attack
Most recently, on July 3, a single cyber gang attacked more than 200 U.S. companies with ransomware, paralyzing their networks just before the Fourth of July weekend. In a similar strategy to the FireEye and SolarWinds attacks last year, the ransomware was carried to the companies’ networks through a network management software package from Kaseya, a popular third-party supplier.
Let that sink in for a moment — 200 companies discovered that the technology they purchased to keep their networks secure was actually the ticking time bomb that was set to detonate just as everyone was going home for the long weekend.
Keeping Your Most Important Documents Secure
Cybersecurity includes a wide range of security precautions and procedures, from training employees not to open questionable email attachments to sophisticated disaster recovery protocols. At the center of all of this is keeping your most vital, confidential documents secure. Implementing reliable and feature-rich legal document management software plays a pivotal role in safeguarding these sensitive files and fortifying overall cybersecurity defenses.
Centralize Document Storage
Businesses can have thousands of important files, but those that are the most important, containing sensitive or confidential information, should be stored in a single, central secure location. This is for three reasons.
First, it ensures that you know exactly where they are located. You don’t have to wonder if your documents are on Server A, Server B or in a VDR.
Second, it allows you to standardize the security you have in place for these types of files, like encryption, digital rights management (DRM) or watermarking.
Third, it allows you to easily restrict access to only those who need access. Even though the files are all stored in a VDR, for example, organizing the files in folders allows you to grant access to some files to one group of stakeholders, while giving access to another folder to a different group of stakeholders.
Encrypt Your Most Important Documents
No one should be able to view the contents of a folder, or the information in a file, if they have not been given authorization. Fortunately, encryption is a seamless experience for those who have been given access to files. When you log in with an authorized account, the files appear without any lag whatsoever. If you don’t have an authorized account, you can’t even see where the folders are, let alone see what’s inside them.
Use Group Permissions Instead of Individual Access
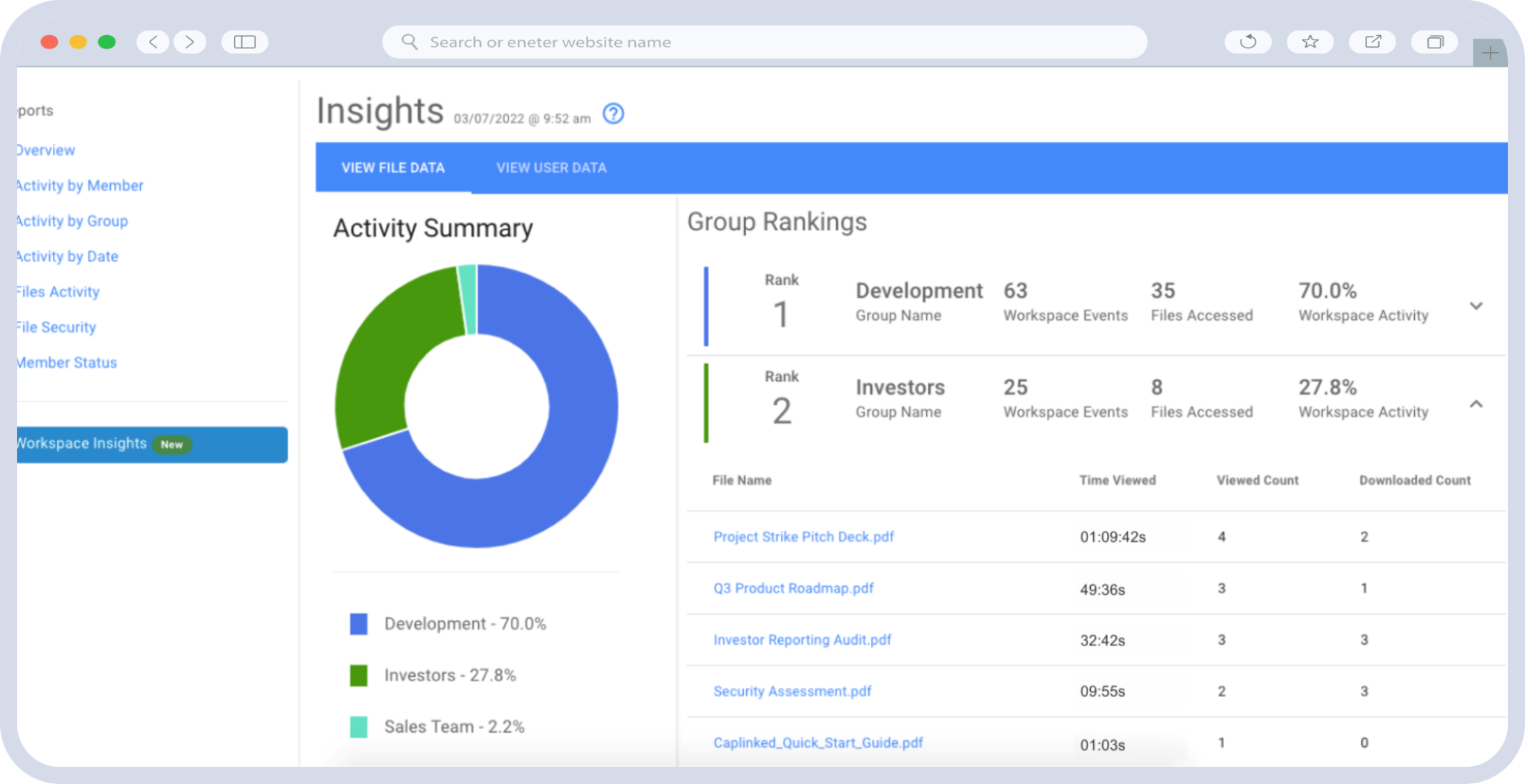
If you don’t establish group access policies, managing user permissions can quickly become more complicated than managing the files themselves. Specify two or three different levels of permissions and then, when you need to grant access to someone, you can simply determine which level of access they should get for each folder.
Use DRM for Your Most Important Documents
Digital rights management software like Caplinked’s FileProtect software, not only lets you specify user access and restrictions, it gives you the ability to track access. You can limit access to the following:
- Authorized users
- Authorized devices
- Authorized IP addresses or geographical regions based on IP addresses
- Specific time periods for accessing documents
- Specific time periods for accessing downloaded documents
Watermark Your Most Important Documents
Another feature that has become standard in modern VDR platforms is digital watermarking. This is particularly beneficial when you need to ensure a secure file transfer and allow people to download or make changes to files. When the file is downloaded, a digital watermark is added to the document that includes the person’s email address and IP address. If there ever is a data leak, the source of the leaked document will be visible directly on that document.
Use a Trustworthy Storage Solution
Caplinked’s virtual data room was built from the ground up with document security in mind. It’s the virtual equivalent to a bank vault for secure storage.
AICPA SOC 2 and EU-US Privacy Shield Certified, it’s also compliant with all HIPAA, PCI SAQ-D, and FISMA requirements. This makes it the trusted document storage solution for any health care, insurance or commercial bank requiring state-of-the-art document storage for their most sensitive documents.
In addition to features like multi-layer security firewalls and a lockdown policy on insecure plugins, Caplinked’s VDR offers a range of additional security features like digital rights management (DRM), digital watermarks and two-factor authentication for secure login access.
To evaluate its security features and explore its user-friendly interface, create a free account and take a closer look.
David Weedmark is a published author and e-commerce consultant. He is an experienced JavaScript developer and a former network security consultant.
Sources
Penta Security: Top 5 AI-powered Cyber Threats & How to Prevent Them
PurpleSec: Cybercrime Up 600% Due To COVID-19 Pandemic
Security Magazine: How to Improve Legal Document Security in Six Steps
Microsoft Azure: Azure Data Security and Encryption Best Practices
Accusoft: Best Practices for Document Management Security
TechTarget: 10 of the Biggest Cyber Attacks of 2020
NPR: A ‘Colossal’ Ransomware Attack Hits Hundreds Of U.S. Companies, A Security Firm Says
New York Magazine: What’s Driving the Surge in Ransomware Attacks?