Identify, Assess, Protect and Monitor: These four simple words have tremendous implications for IT security professionals, and each poses challenges. Real-world security operations may not always be so linear. IT security professionals and cyber-security professionals must be prepared to expect the unexpected, after all.
Knowing the best practices for an organizations information security program at each phase of the life cycle, however, and how they fit together, can help ensure you are protecting the organizations data and network in the best way possible. By standardizing the steps, you make it easier for your team to work together and be more effective in protecting against security breaches. Understanding the risks at each step can help you protect against those risks and better serve your clients or employer.
Table of Contents
ToggleStep 1: Identify What You are Protecting
Every organization is different and may place different values and importance on various data. Financial data, for instance, will almost always require the highest level of security protection. However, cybersecurity begins with the network, so it is important to identify every element of your IT systems that need protecting.
Audit Your Systems
Start the identification process with a complete audit of your systems, enumerating the:
- Routers.
- Servers.
- Firewalls.
- OS.
- Applications and software.
- Physical assets and their locations.
- High-priority, mission critical assets (both physical and digital).
You are ll also want to identify who uses each of the applications and who needs access to them. The danger during the identify phase of the information security life cycle would be speeding through an audit, resulting in inaccuracies. Also, you could misidentify the importance of protection for certain elements of your system, thinking they need less protection than they do. It s important to realistically assess the importance of assets and their security.
Step 2: Assess the Current Security Status of Assets
Once you have identified exactly what assets you are protecting, you want to look at how they are currently being secured. Review your cybersecurity processes and procedures and run the necessary vulnerability scans to identify weak points in your systems.
Take inventory of the tools you are using for your assessment. Are newer, better tools available? Make sure to continue with your documentation so you have complete records of your current protections, allowing you to measure, test and improve.
Pitfalls To Avoid
Don’t over- or under-estimate your current security capabilities. Only with an accurate assessment can you move to stage 3 of the process. Also, as you collect documentation surrounding your security, you will want to keep your inventory of assets, weaknesses, vulnerabilities and strengths as secure as anything else in your organization.
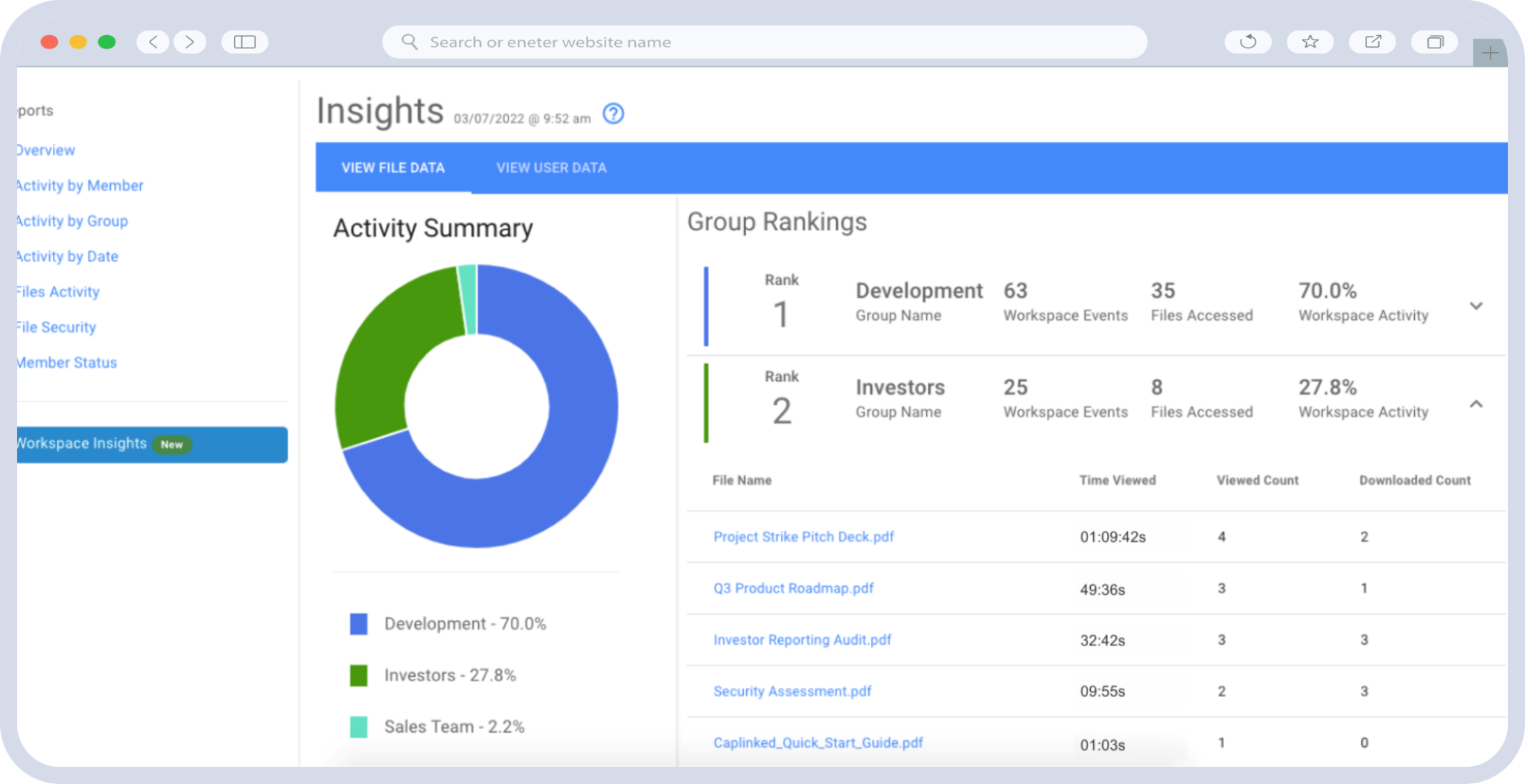
Your IT team can easily collaborate within a virtual data room to share knowledge, files and details and know they are secure as you perform in-depth assessments of your servers and systems.
Step 3: Protect Your Network and Assets
Once you have inventoried and assessed your assets, apps, software, networks and overall IT systems, it is time to move on to the protection phase. With a clear assessment, your risks, weaknesses and vulnerabilities should be obvious. Now it’s time to plug those holes with the right technology.
For larger organizations with hundreds of servers and components, it’s important to take a systematic approach. Begin with smaller, less critical aspects; test; ensure they are bug free and then move on to mission critical systems using the same process. Always stop to test for vulnerabilities and document best practices for replication with each element of your IT systems, from applications to network servers.
Step 4: Monitor Your Systems for Vulnerabilities
Constant monitoring is crucial for continued information security. Continue monitoring your systems for threats, adapting and adopting technology to face new security risks, and reassessing your systems as needed.
When major upgrades are done, you will want to go back to phase one of the information security life cycle to ensure your security systems are standing the test of time. Virtual data rooms like those CapLinked offers can provide a secure, intuitive way to protect mission-critical data, allowing you to check several boxes off your to-do list when it comes to data security.
Dawn Allcot is a full-time freelance writer and content marketing expert specializing in technology, business and finance.
References:
Information Security Today – The Information Security Lifecycle
PlexTrac – The Information Security Lifecycle