Businesses generally grow in one of two ways: organic or inorganic. Organic growth refers to “natural” internal efforts to increase revenues, including launching new products and services, distributing to new markets, increasing brand equity to increase price points, and other initiatives to capture more sales and how to build a security program as part of other initiatives to capture more sales.
On the other hand, inorganic growth is the opposite: working with other companies to fast-track revenues through a combination of measures. Inorganic growth is normally driven by M&A — mergers with or acquisitions by (or of) other companies — or via joint ventures.
“Organic growth tends to be slower, whereas inorganic growth often acts as a booster shot, propelling companies forward,” notes Chris Legg, a senior managing director at Progress Partners.
Table of Contents
ToggleSecure File Sharing as the Path to Inorganic Growth
When companies and their advisors, including bankers, lawyers, accountants, consultants and other professional services providers, seek inorganic growth, they find themselves involved in an M&A transaction. Both companies evaluate each other, via hundreds of documents demonstrating the financial, legal, and operational health of each.
However, these transactions can open the door to a security threat like sensitive data and information leaks or a cyber attack, along with other cybersecurity challenges, including the need for a comprehensive vulnerability assessment. While each company involved with the deal will need to comply with its standard IT security policies, the extremely sensitive nature of the documents under review in an M&A transaction most likely requires adherence to even stricter cyber security policy.
How to Build an Information Security Program & Policy for M&A Deals
Senior management and their advisors need to focus on completing the M&A due diligence process and cannot let security policies stand in the way of a transaction that is expected to result in substantial operational challenges at each of the companies involved.
Instead, companies can lean on a vendor that has these intensive cloud security needs in mind. Caplinked provides virtual data rooms that meet the strictest of standards for security and compliance—regardless of companies’ own internal cyber security policies, processes, or tools in place.
Understand What Sensitive Information Will Need to Be Shared
While some IT teams and MSPs are aware of the need to secure documents as those documents travel outside the organization’s security perimeter, IT professionals or the cyber security team may hold only a broad understanding of the types of sensitive information shared.
Indeed, the documents to be shared outside the company contain the most critical information on which the company operates, such as the following:
- Legal structure, incorporation documents and contracts.
- Records of previous liquidity events, such as private equity transactions or strategic investments.
- Meeting minutes or previous actions by the Board of Directors.
- Business plans.
- Company financials, including profit and loss statements and projections.
- Tax returns, audits, financial valuations and other reports from third-party professional services providers.
- Patents, trademarks, IP and licenses to use those of other companies.
- Product roadmaps.
- Marketing plans and strategies.
- Sales strategy and pipeline, including existing customers, monthly recurring revenue and annual recurring revenue.
- HR data and personal information, including compensation and benefits.
- Technology investments.
- Additional operational liabilities, including capital expenditures, commercial leases and investments in R&D.
Put Policies & Procedures In Place
The IT or cyber security team is certainly involved in the development and implementation of the organization’s security policies, but such policies only take into consideration the organization’s general security needs.
As such, at the time of development of the organization’s security policies, the team might not incorporate the fact that the organization will at some point be involved in a sensitive financial transaction that requires even tighter security measures to be in place.
Unfortunately, M&A and private equity deals are rarely predictable. Further, speed is essential in order for transactions to be evaluated and closed in a timely manner. IT teams, many of which are challenged with fewer resources, cannot be expected to implement a new IT policy and build a new solution the moment senior management alerts them that hundreds of documents need to be shared externally in support of a pending transaction.
Indeed, a robust information security, or infosec, program needs to be in place and ready to accommodate sudden, immediate security needs without disruption.
Leverage a Virtual Data Room (VDR)
While a special information security program can be put in place and used on an as-needed basis when sensitive financial and legal documents are expected to be shared outside the organization, IT will still need to lean on external tools to help them secure documents and data to the tightest of industry standards.
A virtual data room provides these heightened security needs. Standards for virtual data rooms include:
- SOC 1/SSAE 16/ISAE 3402
- SOC 2 Type II
- FISMA, DIACAP and FedRAMP
- HIPAA/ITAR
- DOD CSM Levels 1-5
Leveraging an external provider of secure document solutions can provide additional guidance in the other direction, too. While companies can lean on an external provider like Caplinked, they can present this use case to their own internal IT resources in order to help them develop a stronger infosec program that prepares the company in the future for any potential inorganic growth strategies, such as those involving M&A and any associated due diligence.
Look for API and Third-party Integrations that Create Flexibility
The solution lies with leveraging an API or third-party integration from a provider of secure, cloud-based document sharing solutions. By integrating an API, IT teams and managed service providers (MSPs) can enable the business to quickly and securely share even the most sensitive data without having to build extra required security measures.
The simplicity of connecting existing cloud storage, content management, accounting or financial data systems to an API instantly enables companies to secure their data and documents under the highest standards via AES 256-bit encryption. Files of any type, including Office, PDF and media files, can be protected on any device, thanks to granular permission settings that protect data anywhere it travels.
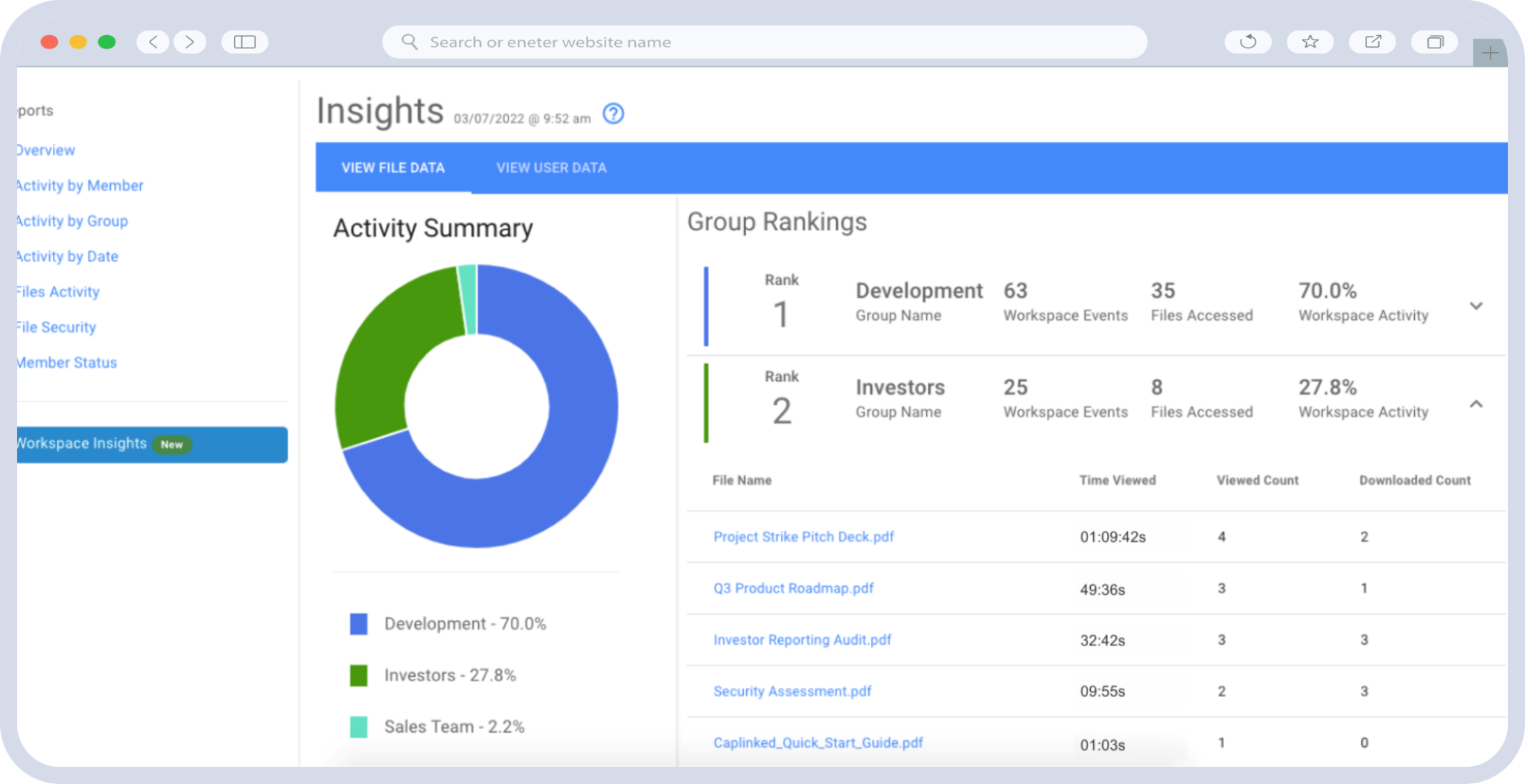
The technology provider should offer a REST API, that can be used in any application written in any language, including Java, Ruby and C++. Leveraging the API enables IT teams and MSPs to see exactly where data has traveled and how it’s being used in real-time. This is useful for companies or teams that require proof of document access.
With end-to-end data encryption, comprehensive activity and file tracking, watermarking ability, plugin-free digital rights management and more.,
With an API from a secure document solution provider like Caplinked gives organizations the flexibility they need to streamline workflows securely — and is the only VDR on the market to offer API capabilities.
Ensure the Security of Your Inorganic Growth Process
As thousands of pages of highly sensitive documents are handled by dozens or hundreds of people in an M&A transaction, privacy, security, and proper access and security controls are necessary to ensure that the right documents are accessed by the right people at the right time.
Organizations should consider an enterprise document management solution with cloud-based document security features, such as Caplinked, that has this goal in mind. Digital rights management capabilities provide encryption and complete control over how a document is used, edited, copied or even printed. Caplinked’s FileProtect feature lets companies share documents while retaining the ability to revoke access from anyone even after it’s been downloaded.
Start your 14-day free trial today!
Jake Wengroff writes about technology and financial services. A former technology reporter for CBS Radio, Jake covers such topics as security, mobility, e-commerce and the Internet of Things.
Sources
TechCrunch – How 2 companies leveraged organic and inorganic growth
BakerTilly – How to break through a business plateau with inorganic growth