In the digital landscape of today’s business world, data transfer and information security have become paramount. As enterprises big and small grapple with how to share and protect sensitive information, one term often comes up in the dialogue — File Transfer Protocol, or FTP.
But is FTP secure? As we delve into the intricacies of data transmission, it’s crucial to understand what FTP is, how it works, and its potential vulnerabilities.
This blog will guide you through the maze of FTP, helping you discern whether it’s a reliable way to transfer data for your enterprise.
Table of Contents
ToggleUnderstanding FTP Security Risks
FTP, or File Transfer Protocol, is an internet protocol that was created to facilitate transferring files over a network. It was initially developed in the 1970s, long before the advent of today’s modern, user-friendly web interfaces. Even though it’s old, FTP is still an important tool in the digital world for both people and businesses.
FTP is frequently used to upload web pages and other kinds of files to a web server. If you have ever uploaded a file to a web hosting account, or downloaded software from a company’s website, chances are you have used FTP to do it. It is also commonly used for sharing files. Instead of sending large files through email or other methods, you can upload them to an FTP server and then provide people with the link to download the file.
Inherent Security Weaknesses of FTP
While FTP was a groundbreaking tool when it was first released, it was unfortunately not designed with robust security measures in mind.
Users and companies often wonder is FTP secure enough for confidential file transfers. The answer is generally no, as FTP doesn’t provide the necessary security measures like encryption and strong authentication.
This has led to several inherent weaknesses such as:
- Data Sent in Clear Text: One of the most significant security weaknesses of FTP is that both the data being transferred and the user credentials (username and password) are sent in clear text. This means that if the transmission is intercepted, the information can be easily read and utilized by cybercriminals.
- No Encryption: FTP clients do not inherently support encryption. This means that data is not scrambled during transmission, leaving it vulnerable to interception and exposure.
- Anonymous Access: FTP servers often allow for anonymous access, meaning that anyone can connect to them. Although this may be advantageous, it also presents a potential entry point for malicious parties.
- Brute Force Attacks Vulnerability: Since FTP requires a username and password, also known as an FTP client, to access the server, it is susceptible to brute force attacks. That’s when a hacker attempts to gain access by trying all possible password combinations until they find the right one.
- Spoofing and Session Hijacking: FTP is also vulnerable to spoofing attacks, where a malicious party impersonates a server or client to gain unauthorized access. Furthermore, because FTP sessions are not encrypted, they can be hijacked, allowing a hacker to take control of the session.
Given these inherent vulnerabilities, it’s essential for businesses to understand the risks associated with using FTP for transferring files and take steps to mitigate them.
FTPS: Enhancing Security with Encryption
File Transfer Protocol Secure (FTPS), also known as FTP Secure or FTP-SSL, is an extension of the standard FTP protocol. The primary distinction lies in the fact that FTPS augments security by utilizing Transport Layer Security (TLS) and Secure Sockets Layer (SSL) protocols. This effectively addresses many of the security shortcomings of the standard FTP.
With FTPS, the information that is transmitted between the client and the server such as usernames, passwords, and the content of files is encrypted. With FTPS, the server and client can authenticate each other, confirming their identities before any data is exchanged. This is a significant advantage over standard FTP, which does not have this authentication process.
SFTP: Secure File Transfer Protocol Explained
The Secure File Transfer Protocol (SFTP) is a new way to send and receive files that’s safer than using SSH. It uses the same underlying secure channel established by SSH to encrypt data and commands, ensuring that information is protected from unauthorized access during transmission. SFTP, unlike FTP, encrypts both commands and data, preventing passwords and other crucial info from being revealed in plain text when transferred over the network.
Implementing Data Security Measures
Hackers use different tricks to break into computer systems through FTP, which is a way to transfer files online.
One trick is called “Anonymous Authentication.” This lets them log in without a real username or password, making it easy for them to access private information. Another method is the “Directory Traversal Attack.” This allows them to sneak into places they shouldn’t be and control files. Then there’s “Cross-Site Scripting,” where they send harmful code through a website to steal personal info. Lastly, there’s the “Dridex-based Malware Attack,” where they trick people into downloading a harmful program that steals banking info. It’s important to stay safe online and keep your information protected from these kinds of attacks.
While FTP has its vulnerabilities, it can be used securely with the right measures in place. Secure alternatives like SFTP and FTPS should be used instead of standard FTP. Regularly updating and patching FTP servers, implementing a strong password policy, and restricting anonymous access are also important. In addition, logging and monitoring FTP sessions can help detect and respond to suspicious activities.
It is imperative to maintain the security of data transfers by regularly updating the protocol. Updates often include patches for known security vulnerabilities, making it harder for attackers to exploit them. An outdated protocol can leave a business exposed to data breaches and other security risks.
Two-Factor Authentication: Strengthening FTP Security
A two-factor authentication technique confirms a user’s identity by employing a combination of two distinct factors: something they know, something they own, or something they are. Although 2FA makes it harder for attackers to gain access, it is most beneficial for individuals than large enterprises. Corporations are often targets of systematic attacks and they require a more robust security approach than 2FA.
Mitigating FTP Vulnerabilities in Enterprises
Large enterprises can mitigate FTP vulnerabilities by using secure alternatives to FTP, implementing strong password policies, regularly updating and patching their FTP servers, and using 2FA. Having a robust incident response plan can also help to quickly respond to any security breaches.
Compliance with data protection regulations is a major challenge for enterprises, especially when using FTP. Regulations like the GDPR and HIPAA require businesses to protect the integrity and confidentiality of data, which can be difficult with FTP due to its inherent security weaknesses.
There have been several high-profile data breaches involving unsecured FTP servers. In 2017, a misconfigured FTP server led to the exposure of personal data of over four million customers of a large telecom company. Similarly, in 2018, an unsecured FTP server was responsible for a data breach at a major healthcare provider, resulting in the exposure of patient records. These incidents underscore the importance of securing FTP servers and implementing robust data security measures.
The Future of Data Transfer: Beyond Traditional FTP
When evaluating peer-to-peer file sharing or general data transfer options, enterprises should always question: is FTP secure? As we saw in the limitations of using FTP as a safe mode of file transfer and how hackers use different tricks to steal information from systems using FTP, there has been a growing demand for secure FTP alternatives. This demand to find FTP alternatives is reshaping the landscape of data transfer.
While FTP has been an essential tool for many businesses, its security vulnerabilities have been exposed time and again. For instance, FTP transfers data in plain text, making it easy for cybercriminals to intercept and manipulate the data while in transit. This vulnerability has resulted in numerous high-profile data breaches, causing significant financial and reputational damage to affected organizations. As a result, the need for a secure FTP alternative has become an urgent priority.
Next-gen Data Transfer Solutions: Virtual Data Rooms
While protocols like FTPS and SFTP provide enhanced security, they come with their own challenges. They have limitations, such as complex setup, firewall compatibility issues, and potential performance slowdowns. This is where Caplinked’s Virtual Data Rooms (VDR) emerge as an alternative FTP solution.
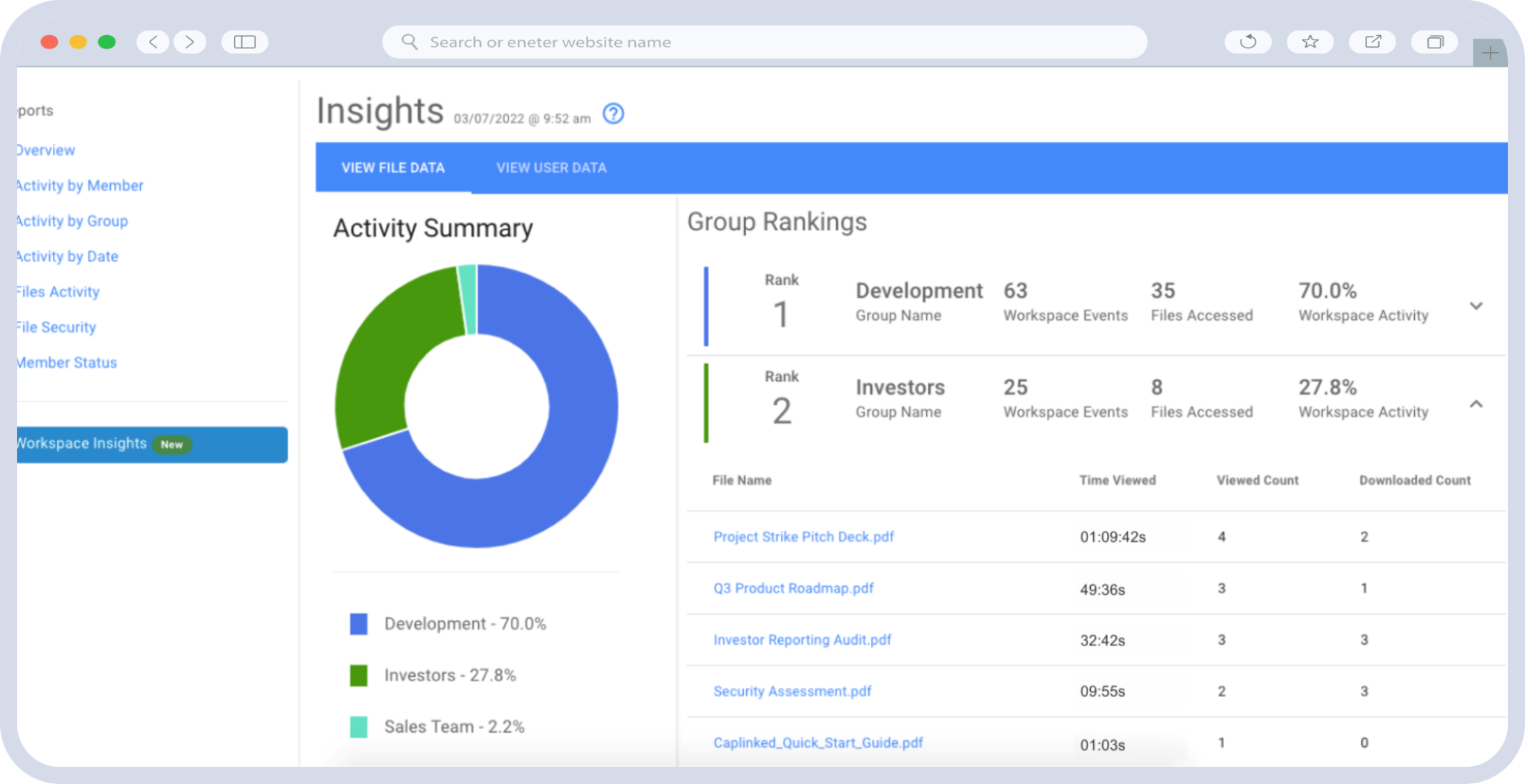
Caplinked’s VDR offers a comprehensive and user-friendly platform for managed file transfer. With advanced encryption and authentication features, Caplinked ensures the utmost security for your sensitive information.
Moreover, Caplinked’s VDR eliminates the complexities associated with traditional FTP alternatives, making it easy to set up and use. It overcomes firewall compatibility issues and delivers optimal performance, ensuring seamless data transfer.
Enhance your VDR experience with comprehensive training for your entire team and 24/7 support. Discover the advantages today by taking advantage of our free trial. Get in touch with us now to get started.
Osheen Jain is a seasoned writer with almost a decade of experience in the fields of technology, science, and business. Her expertise encompasses a diverse range of topics, including B2B SaaS, eCommerce, Data Science, and DevOps.
Sources: