The ability to safely and securely integrate video conferencing into your Virtual Data Room (VDR) is paramount. Because using a VDR obviously indicates that your organization has highly sensitive data to protect (such as in an M&A), the video conferencing solution you choose to use alongside it must have the same robust security requirements.
While video conferencing has come of age in 2020 in the wake of the global COVID-19 pandemic, there have been some bumps along the way regarding quality, reliability — and most importantly, security. Here’s what you need to know.
Table of Contents
ToggleVideo Conferencing Basics
Video conferencing is technology that enables two or more users, no matter where they are on the globe, to be able to engage in meetings together, with both audio and video interaction. It’s usually conducted with computers, but other ubiquitous hardware devices, including smartphones and tablets, are also able to be used to join video meetings.
In the majority of cases, it’s not important what hardware platform is used, but the same software or app has to be employed by everybody participating in the meeting. The most popular video conferencing software packages include Zoom, Skype, FaceTime, GoToMeeting and RingCentral Meetings, but there are scores of other options available.
Common Security Issues
As with any emerging technology that gets adopted on a large scale and very quickly, there was a lot of learning under fire — finding out the issues and flaws of the service and the software as it was being used. For instance Zoom, arguably the most commonly-used package, was constantly in the news for a series of data breaches and “Zoom bombings” — namely people who would randomly enter meeting numbers to try to “crash” a Zoom call.
Early adopters of the technology had no way of anticipating that Zoom bombers would disrupt a call. In order to join a Zoom call, users must click on a link generated by the host of the meeting or would enter a series of numbers that would allow entrance to the meeting. Some organizations would publicly post the link and/or the meeting numbers, which is about as careless as leaving your door unlocked with a large sign indicating your door is, in fact, unlocked. In other cases, some people would attempt to crash meetings by entering random numbers (no doubt using a number generating app) until they stumbled across an unsecured meeting.
In many cases, these were merely harmless pranksters, with no ulterior motive than to disrupt somebody else’s meetings, have a cheap laugh about it and nothing else. However, there were cases of some internet trolls interrupting school sessions and other meetings and engaging in some inappropriate, distasteful and quite often, law-breaking actions, which included lewd behavior, hate speech and screen-sharing of illegal (and sometimes, quite disturbing) images.
In the wake of these Zoom bombings, meeting organizers and participants have tightened up their security, and have refrained from posting meeting numbers and links on public forums; meanwhile, Zoom (along with others) have tightened up the security of these video conferencing apps.
However, for the most part, Zoom is a consumer-oriented software and service that employs minimal security and is generally designed for non-confidential meetings. Now, of course, children using Zoom for school, church services and other types of meetings (an Alcoholics Anonymous meeting, for example) are personal, private and yes, confidential. This privacy shouldn’t be taken any more lightly than your company’s proprietary financial and legal documents.
What To Avoid for Secure Video Conferencing
When it comes to safely incorporating video conferencing into the activity surrounding a VDR and M&A activity, there are some things to steer clear of. Intralinks, which features Zoom integrations that give you the ability to store, catalog and protect your video files in your VDR, is one that definitely should be avoided.
When it comes to proprietary corporate and financial information, the type of documentation and information connected with an M&A, a consumer-level product such as Zoom should not be used in those instances, as it’s vulnerable to the issues described above, even if the updated security measures are enabled.
What To Look For
Three important principles for secure video conferencing are 1) connect securely; 2) to enable access control; and 3) control the ability of attendees to screen share and record the video conference.
- Secure Connection: Relying on a standard home Wi-Fi network is not overly secure. Confirm that high-level security is enabled (WPA2 or WPA3 at a minimum is preferred) and make sure the wireless password is a complex one.
- Access Control: Check your video conferencing security and privacy settings and invited attendees list. Require BOTH a meeting code and a password. Turn on the “waiting room” requirement to avoid any uninvited guests from crashing the meeting. Lock the conference once all attendees have checked in, to avoid any interlopers coming in during your meeting.
- Control File and Screen Sharing: Disable any screen or file sharing privileges to all those except the moderator. Treat any saved video files with the same security protocol as any of the other files in your VDR.
Level Up Secure Video Meets
Secure video conferencing, particularly when it centers around VDR and M&A activity is vitally important. Relying on consumer-level products or using a VDR that integrates with Zoom like Intralinks simply won’t meet the security criteria that both your organization and any others should expect. Protecting your video conferencing is equally as important as safeguarding any of the other documents in your VDR.
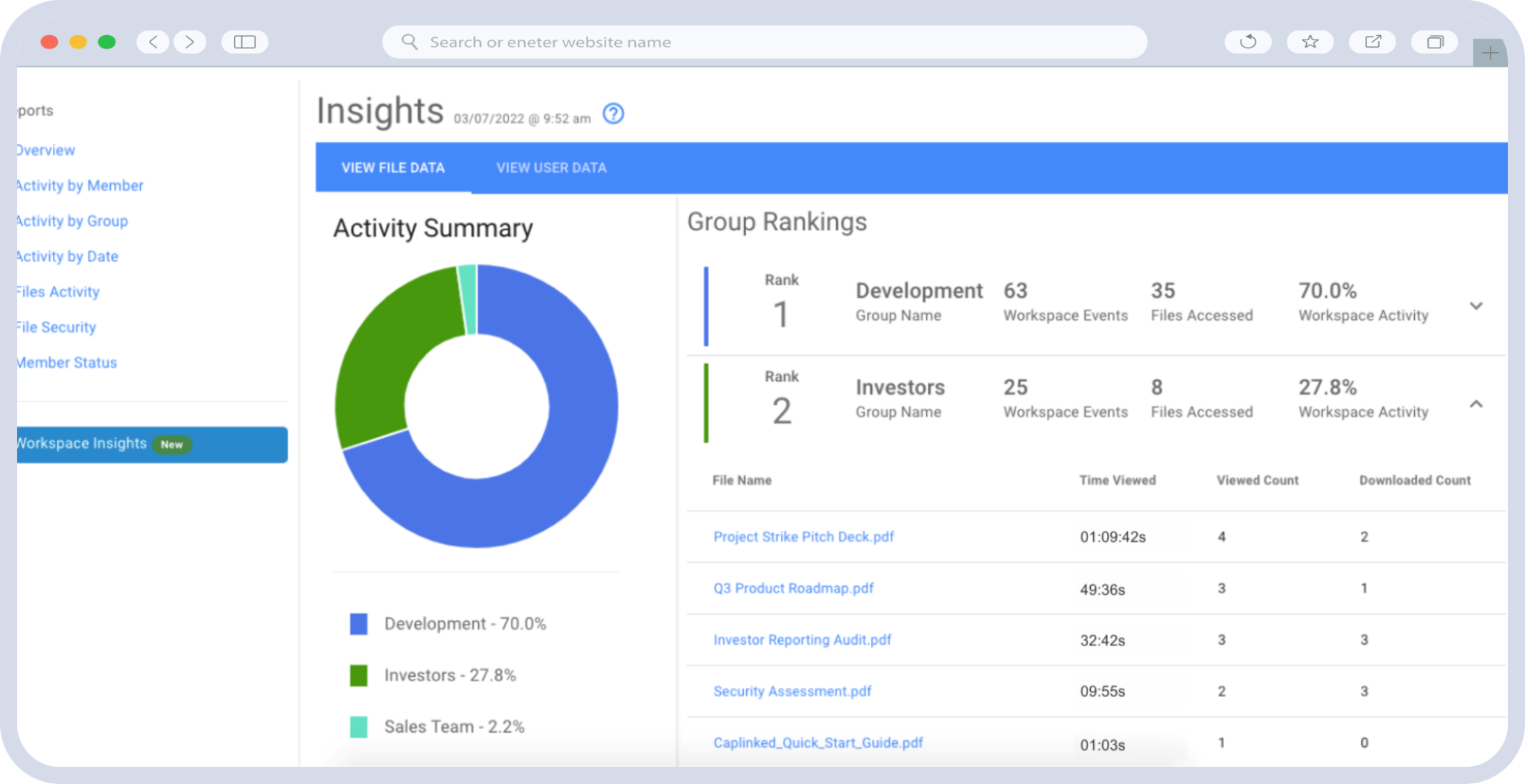
Want to learn more about how to keep your business’s sensitive information safe? Reach out for a free trial of Caplinked today. Our virtual data room software features world-class security, is SSAE16 Type II and ISO 27001 certified, and never integrates with low-security third parties like Zoom.
Chris Capelle is a technology expert, writer and instructor. For over 25 years, he has worked in the publishing, advertising and consumer products industries.