A single data breach during an M&A transaction can destroy deal value, expose trade secrets to competitors, and trigger millions in regulatory penalties. Yet many dealmakers still evaluate virtual data rooms based on features and price alone—overlooking the security certifications and compliance frameworks that actually determine whether their most sensitive deal data is protected. In a landscape where IBM’s 2024 Cost of a Data Breach Report pegs the average breach cost at $4.88 million, understanding virtual data room security is no longer optional. It’s a fiduciary obligation.
This comprehensive guide breaks down the compliance standards, encryption protocols, and security best practices that every M&A professional must evaluate before selecting a VDR. Whether you’re advising on a cross-border acquisition or managing sell-side due diligence, the frameworks outlined here will help you minimize risk, satisfy regulatory requirements, and protect confidential deal information from first disclosure through closing.
Table of Contents
ToggleWhy Virtual Data Room Security Is Critical in M&A Transactions
M&A due diligence security demands are uniquely intense. During a typical transaction, hundreds of confidential documents—financial statements, intellectual property records, employment contracts, customer lists, and proprietary technology specifications—are shared with multiple parties across different organizations, jurisdictions, and time zones. Each document exchange represents a potential attack surface.
The consequences of inadequate virtual data room security extend far beyond immediate financial loss. Leaked deal information can trigger stock price fluctuations, violate securities regulations, compromise competitive positioning, and erode the trust that makes transactions possible. For regulated industries like healthcare, financial services, and defense, a compliance failure during due diligence can halt a deal entirely or invite enforcement action from agencies like the U.S. Securities and Exchange Commission (SEC).
This is precisely why VDR compliance requirements matter: they provide an independently verified framework ensuring that the technology protecting your deal data meets rigorous, internationally recognized standards.
Essential Security Certifications for Virtual Data Rooms
Not all security claims are created equal. Self-reported security features are meaningless without independent verification. The following certifications represent the gold standard in VDR compliance requirements, and every M&A professional should insist on documented proof of these standards before uploading a single document.
ISO 27001: The Global Standard for Information Security Management
ISO 27001 is the world’s most widely recognized certification for information security management systems (ISMS). Published by the International Organization for Standardization (ISO), this framework requires organizations to systematically assess information security risks, implement comprehensive controls, and maintain an ongoing management process that continuously improves security posture.
For M&A professionals, ISO 27001 certification in a VDR provider signals several critical capabilities:
- Systematic risk assessment: The provider has identified and addressed threats specific to document storage and sharing environments.
- Comprehensive control implementation: Over 90 controls across 14 categories—including access control, cryptography, physical security, and incident management—have been evaluated and implemented as appropriate.
- Continuous improvement: Security isn’t a one-time achievement; ISO 27001 requires ongoing surveillance audits, typically conducted annually, to maintain certification.
- Global recognition: Unlike region-specific frameworks, ISO 27001 is recognized and respected across international jurisdictions, making it especially important for cross-border M&A transactions.
ISO 27001 requires organizations to implement a wider range of security controls than many other frameworks, making it particularly robust for environments where highly sensitive financial and legal documents are exchanged.
SOC 2: Trust Services Criteria for Cloud-Based Platforms
SOC 2 (System and Organization Controls 2) is an auditing standard developed by the American Institute of Certified Public Accountants (AICPA) that evaluates a service organization’s controls across five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. SOC 2 reports are tailored to each organization, ensuring that controls and criteria are evaluated in a way that matches the company’s specific services and risk posture.
There are two types of SOC 2 reports that M&A professionals should understand:
- SOC 2 Type I: Evaluates whether appropriate controls are designed and in place at a specific point in time.
- SOC 2 Type II: Evaluates the operational effectiveness of those controls over a defined period (typically 6–12 months). This is the more rigorous and valuable report for assessing a VDR provider.
While ISO 27001 has global applicability, SOC 2 is particularly relevant to the U.S. market and is especially valued by organizations in the technology and financial services sectors. For domestic M&A transactions, a current SOC 2 Type II report is essentially a baseline requirement for any credible VDR provider.
How ISO 27001 and SOC 2 Work Together
These certifications are complementary rather than redundant. ISO 27001 provides a broad, internationally recognized framework for managing information security holistically, while SOC 2 offers a detailed, controls-level audit particularly focused on protecting customer data in cloud environments. A VDR provider holding both certifications has demonstrated security commitment at two distinct levels of scrutiny—and has a significant head start on meeting other compliance standards that clients may require.
Regulatory Compliance Frameworks That Impact VDR Selection
GDPR: Protecting Personal Data in Cross-Border Deals
The General Data Protection Regulation (GDPR), enforced by the European Union since 2018, imposes strict requirements on how personal data is collected, processed, stored, and transferred. For M&A professionals, GDPR compliance in a VDR is critical whenever a transaction involves European entities, employees, customers, or data subjects.
Key GDPR requirements that affect virtual data room security include:
- Data minimization: Only personal data necessary for due diligence purposes should be stored in the VDR.
- Lawful basis for processing: There must be a legitimate legal basis for sharing personal data with prospective buyers or their advisors.
- Cross-border transfer protections: If data moves between EU and non-EU jurisdictions, appropriate safeguards (such as Standard Contractual Clauses) must be in place.
- Right to erasure: The VDR must support the ability to permanently delete personal data when it is no longer needed or when a data subject exercises their rights.
- Breach notification: GDPR requires notification to supervisory authorities within 72 hours of discovering a personal data breach.
With maximum GDPR penalties reaching €20 million or 4% of annual global turnover—whichever is higher—ensuring your VDR provider is GDPR-compliant is not merely a legal nicety but a business imperative for any deal with a European nexus.
HIPAA: Healthcare M&A Considerations
Transactions involving healthcare organizations, health technology companies, or any entity handling protected health information (PHI) must comply with the Health Insurance Portability and Accountability Act. A HIPAA-compliant VDR provides the administrative, physical, and technical safeguards required to protect PHI during due diligence, including encryption, access controls, and audit logging.
Industry-Specific Regulations
Depending on the nature of the target company, additional secure file sharing standards may apply. Financial services deals may implicate requirements from FINRA or the OCC. Defense and government contractor transactions may require compliance with ITAR or FedRAMP. Energy sector deals may involve NERC CIP standards. When evaluating VDR providers, ensure they can accommodate the specific regulatory landscape of your transaction.
Core Technical Security Features to Evaluate
Compliance certifications confirm that a VDR provider meets established standards, but M&A professionals also need to understand the specific technical mechanisms that protect their data. Here are the non-negotiable security features every deal team should verify.
Data Room Encryption: The Foundation of Document Protection
Data room encryption should operate at two distinct levels:
- Encryption in transit: All data moving between users and the VDR must be protected using TLS 1.2 or higher, preventing interception during upload, download, or viewing.
- Encryption at rest: Documents stored on VDR servers should be encrypted using AES-256 encryption, the same standard used by government agencies to protect classified information.
Ask your VDR provider whether they manage their own encryption keys or use a third-party key management service, and whether customer-managed encryption keys are available for organizations with heightened security requirements.
Granular Access Controls and Permission Management
In a typical M&A transaction, different parties need access to different documents at different stages. Effective virtual data room security requires permission controls granular enough to manage access at the individual document level, including:
- Role-based access: Assign permissions based on user roles (e.g., buyer’s counsel, financial advisor, management team).
- Document-level permissions: Control who can view, download, print, or share specific files.
- Dynamic watermarking: Overlay user-identifying information on viewed or printed documents to deter and trace unauthorized sharing.
Time-based access expiration: Automatically revoke access after a specified date or deal milestone.
Comprehensive Audit Trails
Detailed audit logging is both a security feature and a compliance requirement. Your VDR should record every user action—logins, document views, downloads, print attempts, permission changes, and failed access attempts—with timestamps and IP addresses. These audit trails serve multiple purposes: they support regulatory compliance, provide evidence in the event of a dispute, and enable deal teams to analyze buyer engagement and interest levels.
Multi-Factor Authentication (MFA)
Single-factor authentication (username and password alone) is insufficient for protecting M&A deal data. Insist on a VDR that supports multi-factor authentication, requiring users to verify their identity through at least two independent methods before gaining access to sensitive documents.
Secure Infrastructure and Data Residency
Understand where your VDR provider’s servers are physically located and whether they offer data residency options that align with your regulatory requirements. The provider should maintain SOC 2-audited data centers with physical security controls including biometric access, 24/7 surveillance, and environmental protections. Redundant infrastructure and disaster recovery capabilities ensure that deal data remains available even in the event of a system failure.
A Practical Virtual Data Room Security Checklist for M&A Professionals
Use this actionable checklist when evaluating VDR providers for your next transaction:
- Verify current certifications: Request copies of ISO 27001 certificates and SOC 2 Type II reports. Check expiration dates and audit periods.
- Assess GDPR compliance: If European data is involved, confirm the provider’s Data Processing Agreement, data transfer mechanisms, and breach notification procedures.
- Test encryption standards: Confirm AES-256 encryption at rest and TLS 1.2+ encryption in transit.
- Evaluate access controls: Ensure granular, document-level permission management with role-based access, dynamic watermarking, and remote shredding capabilities.
- Review audit trail capabilities: Confirm comprehensive logging of all user activity with exportable reports.
- Confirm MFA support: Verify that multi-factor authentication is available and can be required for all users.
- Examine data residency options: Determine where data will be stored and whether the provider offers jurisdiction-specific hosting.
- Review incident response procedures: Ask about the provider’s breach detection, response, and notification protocols.
- Assess uptime and reliability: Request historical uptime statistics and understand the provider’s disaster recovery and business continuity plans.
Check third-party penetration testing: Confirm that the provider undergoes regular, independent penetration testing and vulnerability assessments.
Best Practices for Maintaining VDR Security Throughout a Deal
Selecting a secure VDR provider is necessary but not sufficient. M&A due diligence security also depends on how deal teams use the platform. Follow these best practices to maximize protection throughout the transaction lifecycle:
Establish a Clear Data Governance Policy
Before uploading any documents, define and document your data governance framework. Specify who has authority to grant access, what categories of documents will be shared at each deal stage, how personal data will be handled in compliance with applicable regulations, and what happens to data when the deal closes or terminates.
Apply the Principle of Least Privilege
Grant each user only the minimum access necessary for their role in the transaction. Avoid blanket permissions that give all parties access to all documents. Use staged disclosure, releasing additional documents as the deal progresses and parties demonstrate continued interest and commitment.
Conduct Regular Access Reviews
As deal teams evolve—advisors change, parties drop out, new stakeholders join—access permissions must be updated promptly. Conduct weekly reviews of user access during active due diligence periods, and immediately revoke access for any individual who no longer has a legitimate need.
Train All Users on Security Protocols
The most sophisticated VDR security features are undermined by human error. Ensure all deal team members understand how to use the platform securely, recognize phishing attempts, and comply with the transaction’s confidentiality requirements. Even a brief onboarding session can significantly reduce the risk of accidental data exposure.
Plan for Post-Deal Data Management
Define your data retention and destruction policy before the deal concludes. Determine how long documents will remain accessible after closing, who retains archive access, and when data will be permanently deleted. A strong VDR provider will support automated data retention policies and certified data destruction.
How CapLinked Delivers Enterprise-Grade Virtual Data Room Security
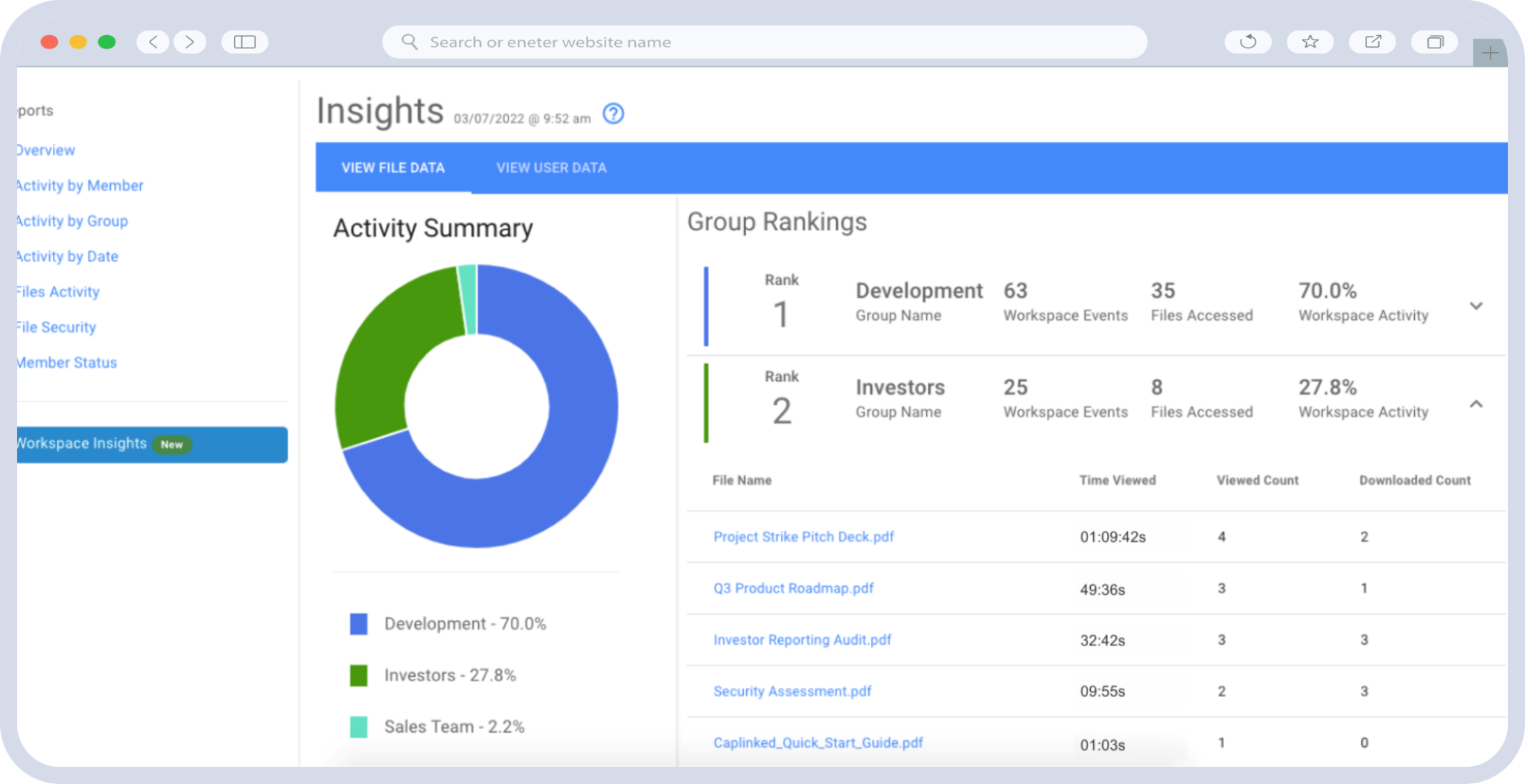
CapLinked’s virtual data room platform is purpose-built for the security demands of M&A transactions, capital raises, and other high-stakes business events. With robust encryption, granular access controls, comprehensive audit trails, and compliance with leading security frameworks, CapLinked gives dealmakers the confidence that their sensitive data is protected at every stage.
From dynamic watermarking and document-level permissions to detailed activity tracking and secure infrastructure, CapLinked’s platform is designed to meet the VDR compliance requirements that sophisticated deal teams demand. Whether you’re managing a domestic acquisition or a complex cross-border transaction, CapLinked provides the secure file sharing standards your deal requires.
Ready to protect your next transaction with enterprise-grade virtual data room security? Start a free trial with CapLinked and experience the security, compliance, and control that M&A professionals trust for their most sensitive deals.
Frequently Asked Questions
Virtual data room security encompasses the encryption, access controls, audit trails, compliance certifications, and infrastructure protections that safeguard sensitive documents shared during M&A transactions. It matters because due diligence involves sharing highly confidential financial, legal, and operational data with multiple external parties, and a security failure can destroy deal value, violate regulations, and expose trade secrets. Robust virtual data room security ensures that only authorized individuals can access specific documents, that all activity is logged, and that data is protected both in transit and at rest.
At minimum, a virtual data room should hold ISO 27001 certification and a current SOC 2 Type II report. ISO 27001 is the globally recognized standard for information security management systems, while SOC 2 Type II verifies that security controls are operationally effective over time. For deals involving European data, GDPR compliance is also essential. Depending on the industry, additional standards like HIPAA (healthcare), FedRAMP (government), or FINRA requirements (financial services) may apply.
Data room encryption protects deal documents at two levels: AES-256 encryption secures files stored on VDR servers (encryption at rest), while TLS 1.2 or higher protects data as it moves between users and the platform (encryption in transit). Together, these encryption standards ensure that even if data is intercepted or servers are compromised, the information remains unreadable to unauthorized parties. AES-256 is the same encryption standard used by government agencies for classified information.
ISO 27001 is an international standard that certifies an organization's entire information security management system, requiring a broad range of controls across multiple security domains. SOC 2 is a U.S.-based auditing framework that evaluates specific controls related to security, availability, processing integrity, confidentiality, and privacy. ISO 27001 has global applicability and requires implementation of more comprehensive controls, while SOC 2 is tailored to each organization's services and is particularly relevant for cloud-based platforms. The strongest VDR providers hold both certifications.
To ensure GDPR compliance in a virtual data room, confirm that the provider offers a Data Processing Agreement, supports data residency in EU-approved jurisdictions, and implements Standard Contractual Clauses for cross-border data transfers. The VDR should also support data minimization principles, the right to erasure, and breach notification within 72 hours. M&A professionals should work with legal counsel to establish a lawful basis for processing personal data during due diligence and limit the personal data uploaded to only what is strictly necessary.
M&A professionals should prioritize virtual data room security features including AES-256 encryption at rest, TLS 1.2+ encryption in transit, granular document-level access controls, multi-factor authentication, dynamic watermarking, comprehensive audit trails, remote access revocation, and automated data retention policies. Additionally, the VDR provider should undergo regular third-party penetration testing and maintain SOC 2-audited data centers with physical security controls, redundancy, and disaster recovery capabilities.