There are two things information security consultants are all-too-familiar with seeing:
- The look of despair on a client’s face just after they’ve suffered a network security breach.
- How that same client appears when their network security gaps are remediated, and they discover new ways for secure document sharing.
Just like with any technology, security measures are only as effective as the policies and practices applied to using them. It only takes a temporary lapse of judgment with the information security policy, or a simple misunderstanding by a well-meaning employee to expose sensitive files, company intel, or your customers’ confidential data to opportunistic hackers. (Another common mistake is assuming VDRs and Dropbox are interchangeable.)
Table of Contents
ToggleWhat Is Information Security?
Information security, or infosec, encompasses the policies and practices that protect an organization’s data from any unauthorized access or unauthorized usage. Information security management encompasses data that is being stored as well as being transmitted from one place to another.
Since computer-based information is always stored as electronic data, an information security program is usually synonymous with data security, although both can include paper-based information too — like report printouts and those passwords employees still keep on sticky notes in their drawers.
Unauthorized usage is an important distinction in information security management, as many people believe security starts and ends with access. To define information security more specifically, it includes preventing unauthorized actions, such as the following, to any confidential, private or sensitive information:
- Access
- Usage
- Inspection
- Disclosure
- Disruption
- Modification
- Recording
- Destruction
This information security program includes company trade secrets, financial records and audit logs, as well as personal information belonging to clients, suppliers and employees — from credit card numbers to private social media photos.
The Difference between Cybersecurity and Information Security
Any other data security terms you might hear are almost always a subdiscipline of information security. Cryptography, for example, refers to how data is encrypted to keep it secure.
Cybersecurity is also a subset of information security. As Cisco explains, it’s the practice of protecting systems from digital attacks, including websites, databases and computer networks. In this case, the word “cyber” in a cybersecurity plan refers to how people are accessing the information, regardless of where the information is — i.e., cyberattacks.
Antivirus software, malware protection, DNS filtering and firewalls are all cybersecurity protections. There are three points of entry that a security plan should protect:
- Computers, mobile devices and routers
- Computer networks
- Cloud (internet transmissions and storage)
Information security encompasses all of these things, but also includes hardware and software protection like encryption and locked server rooms. It also includes awareness training for users on proper security practices.
Common Threats to Information Security
Threats to information security today are far too numerous to list. Just take a look at the scan log on your antivirus program to get an idea of how many there are. Most, however, can be placed in four broad categories:
- Malware, like viruses, worms, trojans and bots
- Ransomware and scareware
- Adware and spyware
- Rootkits: tools to gain administrative privileges in a system
Of course, these aren’t threats unless your system defenses are down, or unless you’re not aware of them. Having an effective information security plan in place is your best defense against these threats and the new ones that will be arriving in the near future.
Six Ways to Improve Your Information Security Plan
Here are five practices you can build into your company’s information security strategy. When your information security policy is executed correctly, they’ll save your firm a great deal of stress and money, and they’ll also safeguard your reputation.
1. Encrypt all Data Stored in the Cloud
Simply put, encryption protects your data, whether it’s stored in a data center or being transmitted around the internet. Encryption protects your data from all unwanted eyes, including those of business partners, competitors, malicious hackers and even regular people who have no business knowing your company’s sensitive information. Encryption is most effective when it’s ubiquitous and integrated into your existing workflow; you shouldn’t have to turn on/off data encryption. It should be an automatic process when sharing files via the cloud.
Look for cloud solutions that offer the strongest block ciphers available and 256-bit advanced encryption, and that meet industry security compliance standards, such as the following:
- PCI DSS
- AICPA SOC 2
- ISO 27001
Not only do these security standards help protect your sensitive data, they also demonstrate to potential clients that you take information security seriously, establishing trust and credibility in your industry.
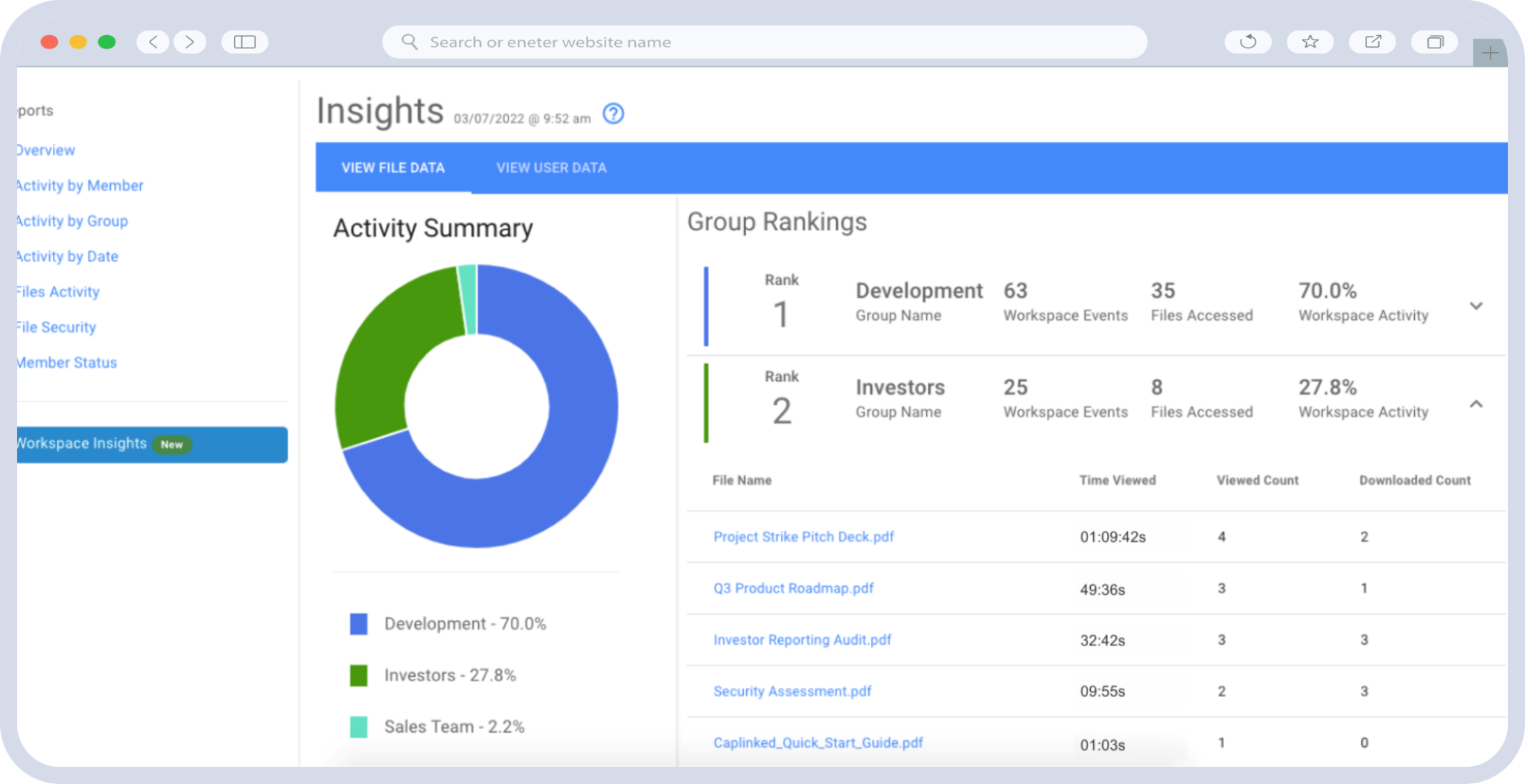
2. Manage File Access Permissions
Although data breaches from external attacks often get the biggest headlines, data loss is often a result of employee error. Define who needs to have access to specific client data, how to remove permissions should an employee leave the business, ensure two-factor authentication is being used, and that the permission rights your staff should have to print, email, export or save documents outside of your designated cloud or on-premises software.
If an attorney, account manager, finance administrator or other employee isn’t involved in the day-to-day interactions with a client, or doesn’t need oversight into the process of that business, they shouldn’t have rights to view, delete or even know that certain files exist. Keep a tight line of permissions around those sorts of files, and the likelihood of data leaking drops rapidly. Also consider using an Enterprise Digital Rights Management solution to help control assets that need to be sent outside of the security perimeter.
3. Protect Data Across all Applications and Devices
It’s a real double-edged sword: Laptops and mobile devices equipped with cloud applications make it easy to access files from outside the office, helping move business forward despite physical boundaries. However, file sharing outside your network firewall, especially via the cloud, introduces a number of vulnerabilities to your information.
You can establish policies on the sorts of files that can be accessed outside the office. Or, you can adopt a data protection system that offers secure mobile applications for Android or iOS devices. Do your employees or customers prefer to use cloud services like Dropbox or Office 365 for email and client files? Virtual data room applications integrated to these cloud services increase adoption and appreciation for secure collaboration. Make sure your online file sharing service is secure, though — cybersecurity matters in every aspect of your business that takes place on the internet.
4. Stay Current on News and Trends
Hackers never sleep. New malware, vulnerabilities and “zero day” attacks occur frequently. Don’t let malicious attackers, or even your competitors, get their hands on information that is critical to your business or the privacy of your clients. Companies that are dedicated to managing the private affairs of other organizations and individuals often have the largest targets on their backs.
Keep up to date on the latest strengths, weaknesses, opportunities and threats by following the Caplinked blog and other reputable infosec news sources, especially Twitter, which can provide near live updates as data breach stories emerge. Knowledge is the key to protecting your company against data leaks, so make sure to keep your entire organization up to speed on new technology and vulnerabilities.
5. Train Employees on Security Best Practices
A significant aspect of bolstering your information security plan is investing in comprehensive training for your employees on security best practices. Human error or lack of awareness can often lead to security incidents.
It is crucial to educate your staff on the importance of strong passwords, recognizing phishing emails, and following company policies and procedures related to information security. Regular training sessions should be conducted to keep the employees updated on the latest cybersecurity threats and how to protect themselves and the organization from these threats.
Additionally, creating a culture of security within the organization can significantly reduce the risk of data breaches and other security incidents. This involves making security a part of the company’s core values and ensuring that every employee understands their role in protecting the organization’s information assets. By doing so, you are not just protecting your company’s data, but also reinforcing your commitment to safeguarding your clients’ sensitive information, thereby enhancing your firm’s reputation and credibility in the industry.
6. Have a Plan of Action
Once the network perimeter is in place and cloud applications are secured, you still have to devise a strategy for what you should do if a security breach takes place. A dedicated team needs to define the following:
- What information assets exist, and where/how are they managed now?
- Who are the prime points of contact (internally and externally) should a breach occur?
- What is the communication plan to customers, should a breach occur?
- Are there financial, technical and/or backup resources for remediation in case of a breach to ensure business continuity?
As with many things in life, when you fail to plan, plan to fail. If your company experiences data loss, your recovery and containment activities speak volumes to customers and internal stakeholders.
Information security isn’t a project with finite beginning and end dates. Solidify and streamline your policy, communicate it to all employees, and consistently review and test it to ensure your entire organization is keeping up with emerging threats.
Interested in taking the first step to improving your organization’s information security plan? Sign up for a free trial of Caplinked’s award-winning virtual data room today.
Sources:
https://www.geeksforgeeks.org/what-is-information-security/
https://www.cisco.com/c/en_ca/products/security/what-is-cybersecurity.html
https://digitalguardian.com/blog/top-50-infosec-blogs-you-should-be-reading
https://www.geeksforgeeks.org/threats-to-information-security/?ref=rp