Every M&A transaction hinges on a paradox: you must share your most sensitive financial, legal, and operational documents with outside parties — while ensuring those documents never fall into the wrong hands. A single data breach during due diligence can collapse a deal, trigger regulatory penalties, and destroy years of built enterprise value. Yet when deal teams evaluate virtual data room providers, they often rely on marketing buzzwords rather than verifiable security capabilities. This guide cuts through the noise. Below, we demystify the technical and compliance aspects of virtual data room security, giving deal teams and executives actionable criteria for evaluating VDR platforms based on what actually protects their data — not what sounds impressive on a sales deck.
Table of Contents
ToggleWhy Virtual Data Room Security Is Non-Negotiable in M&A Transactions
Mergers and acquisitions involve the exchange of vast amounts of confidential information: audited financials, intellectual property portfolios, employment agreements, customer contracts, pending litigation files, and strategic projections. Unlike generic file-sharing platforms, a virtual data room provides a secure, controlled, and fully traceable environment purpose-built for these high-stakes exchanges.
The consequences of inadequate M&A due diligence security are well documented. According to the IBM Cost of a Data Breach Report 2024, the global average cost of a data breach reached $4.88 million — a figure that escalates significantly in regulated industries like financial services and healthcare. For deal participants, the risk extends beyond direct financial loss to include regulatory enforcement, reputational damage, and the potential unwinding of completed transactions.
Virtual data rooms mitigate these risks by combining multiple layers of protection: encryption at rest and in transit, granular permission structures, real-time activity monitoring, and compliance certifications verified by independent auditors. Understanding each layer — and knowing which questions to ask — is essential for any executive or advisor responsible for safeguarding deal information.
Core Virtual Data Room Security Features Explained
Not all VDR platforms are created equal. The features below represent the baseline requirements for any virtual data room used in M&A transactions. When evaluating providers, confirm that each capability is not only present but independently validated.
Data Encryption: The Foundation of Secure File Sharing
Secure file sharing encryption is the single most critical technical control in any virtual data room. Encryption transforms readable data into ciphertext that is unintelligible without the correct decryption key, protecting documents both when they are stored on servers (at rest) and when they travel between users (in transit).
Look for providers that use AES-256 encryption at rest and TLS 1.2 or higher for data in transit. More importantly, ask whether the provider’s encryption modules have been validated under FIPS 140-2 or FIPS 140-3 — the federal standard published by the National Institute of Standards and Technology (NIST). FIPS validation means a government-accredited laboratory has tested and certified the encryption implementation, not merely that the provider claims to use a particular algorithm.
This distinction matters. A provider can use AES-256 and still implement it incorrectly. FIPS validation eliminates that ambiguity and is often a prerequisite for transactions involving government contracts, defense-related assets, or regulated financial institutions.
Granular Access Controls and Permissions
Encryption protects data from outsiders. Data room access controls protect data from insiders who should not see certain documents — or who should see them only under specific conditions. Effective access controls in a VDR go far beyond simple username-and-password gating.
- Role-based permissions: Assign access at the user, group, or role level. For example, a potential acquirer’s legal team might have view-only access to litigation files, while the financial advisory team sees only the financial exhibits.
- Document-level controls: Set permissions at the individual document or folder level, not just at the room level. This prevents overexposure when multiple workstreams share a single data room.
- View-only access with download restrictions: Allow users to review documents within the VDR interface without downloading, or printing them.
- Dynamic watermarking: Overlay user-identifying information on viewed documents to deter unauthorized photography or distribution.
- Time-limited and revocable access: Set expiration dates on permissions and instantly revoke access when a party exits the deal or a phase concludes.
These controls are especially important in competitive auction processes, where multiple bidders access the same data room but must be prevented from seeing one another’s activity or accessing information beyond their authorized scope.
Multi-Factor Authentication (MFA)
Passwords alone are insufficient. Multi-factor authentication requires users to verify their identity through at least two independent methods — typically something they know (a password) and something they have (a code generated by a mobile app or sent via SMS). MFA dramatically reduces the risk of unauthorized access from compromised credentials, which the Verizon 2024 Data Breach Investigations Report identified as a factor in the majority of web application breaches.
When evaluating VDR providers, confirm that MFA is mandatory — not optional — and that it supports modern authentication protocols such as TOTP (time-based one-time passwords) and integration with enterprise single sign-on (SSO) systems.
Comprehensive Audit Trails
An audit trail is a chronological, tamper-evident log of every action taken within the virtual data room: who accessed which document, when, from what IP address, for how long, and whether they downloaded, printed, or forwarded it. Audit trails serve three critical functions in M&A transactions:
- Regulatory compliance: Demonstrate to regulators that sensitive data was handled in accordance with applicable laws and that access was appropriately restricted.
- Dispute resolution: Provide definitive evidence of what was disclosed, to whom, and when — critical in post-closing disputes over representations and warranties.
- Security monitoring: Detect anomalous behavior in real time, such as bulk downloads at unusual hours or access from unexpected geographies.
Automated, granular audit logs are not merely a back-end feature; they are a cornerstone of deal governance. Ensure your VDR provider generates audit reports that are exportable, searchable, and detailed enough to satisfy both internal counsel and external regulators.
Information Rights Management (IRM) and Document Controls
Advanced VDRs extend protection beyond the data room itself through information rights management. IRM controls travel with the document, enforcing security policies even after a file has been downloaded. This includes the ability to remotely revoke access to downloaded documents, prevent copy-paste actions, disable printing, and apply persistent watermarks.
For law firms managing attorney-client privileged materials, IRM capabilities — combined with possessionless editing features that maintain chain of custody — are particularly valuable. They allow secure collaboration with clients and opposing counsel without relinquishing control over privileged content.
VDR Compliance Standards You Should Verify
Security features are only as credible as the frameworks that validate them. VDR compliance standards provide independent, third-party assurance that a provider’s controls meet recognized benchmarks. Below are the certifications and regulatory frameworks most relevant to M&A transactions.
SOC 2 Type II
A SOC 2 Type II report, governed by the American Institute of Certified Public Accountants (AICPA), evaluates a service provider’s controls over security, availability, processing integrity, confidentiality, and privacy over a sustained period — typically six to twelve months. Unlike a SOC 2 Type I report, which assesses controls at a single point in time, a Type II report demonstrates that controls are operating effectively on an ongoing basis. This is the gold standard for SaaS security assurance and should be a non-negotiable requirement for any VDR used in M&A.
ISO 27001
ISO 27001 is the international standard for information security management systems (ISMS). A VDR provider with ISO 27001 certification has implemented a comprehensive, risk-based approach to managing sensitive information — including policies, processes, and technical controls — and has been audited by an accredited certification body. While SOC 2 is more common in North America, ISO 27001 is widely recognized globally and is particularly important for cross-border transactions.
GDPR, CCPA, and Data Privacy Regulations
M&A transactions frequently involve the transfer of personal data — employee records, customer databases, and vendor information. The EU General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) impose strict requirements on how personal data is collected, processed, stored, and transferred. Your VDR must support compliance with these frameworks through features such as data residency controls (choosing where data is physically stored), consent management, data subject access request facilitation, and the ability to permanently delete data upon deal completion.
HIPAA, GLBA, and Industry-Specific Regulations
Transactions involving healthcare entities must comply with HIPAA requirements for protected health information. Financial services deals fall under the Gramm-Leach-Bliley Act (GLBA) and, for public companies, the Sarbanes-Oxley Act (SOX). Ask VDR providers which industry-specific regulations their platform is designed to support and request documentation — not just a checkbox on a marketing page — demonstrating how specific features map to specific regulatory requirements.
How to Evaluate Virtual Data Room Security: An Actionable Checklist
Marketing claims are easy to make. Use the following checklist to evaluate VDR providers based on substance rather than rhetoric:
- Request the SOC 2 Type II report. Any reputable provider will share this under NDA. Review the auditor’s findings, not just the certification logo.
- Verify encryption standards. Ask specifically: “Is your encryption module FIPS 140-2 or FIPS 140-3 validated?” Request the NIST certificate number.
- Test access controls in a trial environment. Set up multiple user roles with different permission levels and verify that restrictions are enforced as configured.
- Review the audit trail. Generate a sample audit report and confirm it captures document-level actions, user identities, timestamps, IP addresses, and session durations.
- Ask about data residency. Where are servers located? Can you select specific geographic regions to comply with data sovereignty requirements?
- Evaluate MFA implementation. Is MFA enforced for all users by default, or can individual users opt out?
- Assess incident response capabilities. What is the provider’s SLA for notifying customers of a security incident? Do they maintain a documented incident response plan?
- Confirm data deletion policies. After a deal closes, how is data purged? Can you obtain a certificate of destruction?
This checklist transforms the VDR evaluation process from a subjective comparison of feature lists into an objective, evidence-based assessment. Share it with your legal, compliance, and IT stakeholders to ensure alignment across the deal team.
Common Mistakes Deal Teams Make with VDR Security
Even with a capable VDR platform, human error remains the leading cause of data exposure. Avoid these common pitfalls:
Over-Permissioning Users
Granting all bidders access to the entire data room on day one is a common shortcut that creates unnecessary risk. Instead, stage access by deal phase and bidder tier. Use folder-level permissions to release information progressively as parties advance through the process.
Neglecting User Training
A VDR’s security features are only effective if users understand and follow them. Brief all participants — internal team members and external advisors — on the platform’s security protocols, including MFA setup, document handling policies, and the consequences of non-compliance.
Ignoring Audit Logs Until a Problem Arises
Audit trails are most valuable when monitored proactively. Designate a team member to review access logs at regular intervals during the deal process. Look for anomalies: unexpected access patterns, bulk downloads, or logins from unfamiliar locations. Early detection can prevent a minor oversight from becoming a material breach.
Using Consumer-Grade File Sharing for Overflow
When a VDR’s storage limits are reached or a quick share is needed, deal teams sometimes resort to email attachments or consumer file-sharing services. This creates unmonitored, unencrypted copies of confidential deal materials outside the controlled environment. Ensure your VDR plan includes sufficient storage and that all participants understand the prohibition on out-of-platform sharing.
Why CapLinked for Secure M&A Due Diligence
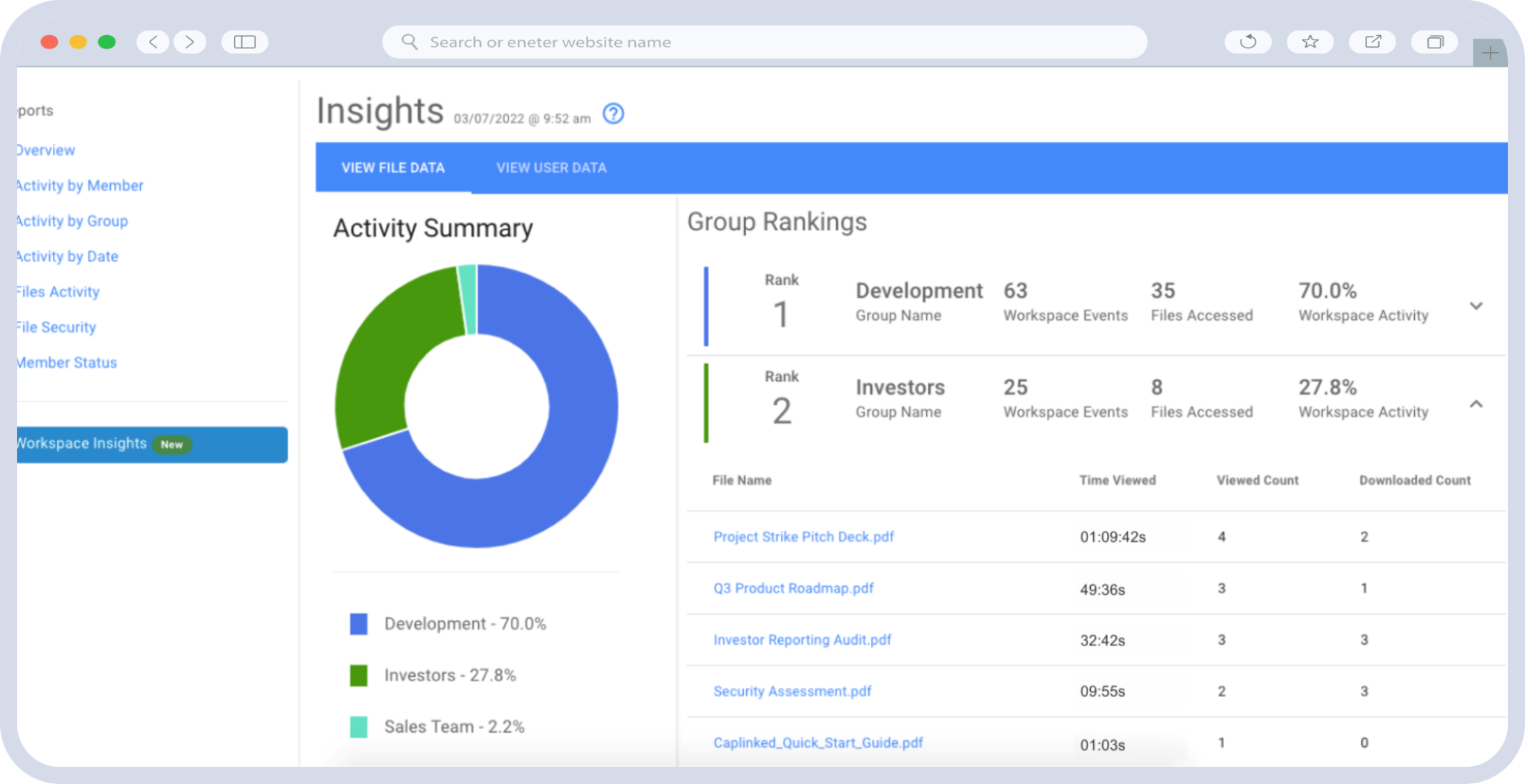
CapLinked’s virtual data room platform is built specifically for the security and compliance demands of M&A transactions, capital raises, and other high-stakes business processes. With enterprise-grade encryption, granular access controls, comprehensive audit trails, and compliance with leading industry standards, CapLinked gives deal teams the confidence that their sensitive documents are protected at every stage of the transaction.
Whether you are a sell-side advisor managing a competitive auction, a buyer conducting due diligence across multiple targets, or a compliance officer ensuring regulatory adherence, CapLinked provides the security infrastructure your deal requires.
Ready to see how CapLinked protects your most sensitive deal data? Request a demo today and evaluate our security features firsthand — with a trial environment, full audit trail access, and a team that can answer every question on this checklist.
Frequently Asked Questions
Virtual data room security refers to the combination of encryption, access controls, authentication protocols, audit trails, and compliance certifications that protect confidential documents shared during M&A transactions. It matters because M&A due diligence involves exchanging highly sensitive financial, legal, and operational information with outside parties, and a security failure can result in data breaches, regulatory penalties, deal collapse, and significant financial loss.
The essential virtual data room security features include AES-256 encryption at rest with TLS 1.2+ in transit, FIPS 140-2 or 140-3 validated encryption modules, granular role-based and document-level access controls, mandatory multi-factor authentication, comprehensive audit trails that log all user activity, dynamic watermarking, and information rights management (IRM) that enforces security policies on downloaded files. These features work together to prevent unauthorized access, deter insider misuse, and provide an evidence trail for compliance.
A virtual data room used for M&A should hold a SOC 2 Type II certification, which demonstrates that security controls are independently audited and operating effectively over time. ISO 27001 certification is important for cross-border deals. The platform should also support compliance with data privacy regulations such as GDPR and CCPA, and industry-specific frameworks like HIPAA for healthcare deals and GLBA for financial services transactions.
Data room access controls protect deal documents by restricting who can view, download, print, or edit specific files based on their assigned role or permission level. Granular controls allow administrators to set permissions at the individual document or folder level, enforce view-only access without download rights, apply dynamic watermarks, set time-limited permissions, and instantly revoke access when a party exits the deal. This prevents overexposure and ensures each participant sees only the information they are authorized to access.
Virtual data rooms are purpose-built for high-stakes transactions and offer security capabilities that consumer file-sharing platforms lack. These include granular document-level permissions, mandatory multi-factor authentication, detailed audit trails tracking every user action, dynamic watermarking, information rights management on downloaded files, and compliance certifications such as SOC 2 Type II and ISO 27001. Consumer platforms are designed for convenience and collaboration, not for the controlled, traceable, and compliant document sharing required during M&A due diligence.
Yes. A virtual data room's audit trail provides a tamper-evident, chronological record of every document accessed, by whom, when, and what actions were taken. This detailed log serves as definitive evidence in post-closing disputes over representations and warranties, demonstrating exactly what was disclosed and to which parties. During regulatory audits, these same logs demonstrate compliance with data handling requirements under frameworks such as SOX, GDPR, and GLBA.