Your company’s intellectual property (commonly referred to as “IP”), is an undeniably important asset. Though usually intangible, IP and IP assets are commonly far more valuable than most of the other physical assets of your company. Therefore, knowing how to protect intellectual property is just as important (or more so) than locking your office and other facilities at the end of the day.
In this article, we’ll explore how to effectively protect your IP and intellectual property rights, the technological options that are available for IP protection, and how to leverage today’s secure options against protecting intellectual property infringement, such as secure virtual data rooms.
Table of Contents
ToggleWhat Is Intellectual Property?
Intellectual property (IP) is a class of assets that are the products of original, creative thought. There are many types of intellectual property, including patents, trademarks, copyrighted material, industrial designs, geographical indications and trade secrets.
Naturally, intellectual property assets are hugely valuable — IP assets are often the product of years of research and development, as well as large sums of capital invested into them over the years. In many situations, intellectual property is the greatest asset of a company.
In most instances, IP falls under one of the following categories of intellectual property law:
- Copyrights: The rights that creators (or owners) of creative works — written, musical, artistic or visual ‑ have over their work. For example, the material in a book is copyrighted, which forbids non-owners from publishing (or for profiting) from that material.
- Patents: The right (issued by a governmental agency) given to an inventor (or owner) of a product or process that protects it from others making (or profiting from) the same item.
- Trademarks: Often referred to as “service marks,” trademarks typically are a product name, graphic element or even a catchphrase, which distinguishes an item (usually a brand) from other similar products. Most major brands have a trademarked brand name as well as a trademarked logo.
- Industrial designs: Industrial design (or “ID”) is the design process of products with the goal of manufacturing a mass-produced product. ID creates products that are unique and distinguishable from similar products. The iPhone is a classic example of ID.
- Geographical indications: An indicator that a product is very specific in its origin. An example would be champagne, which is sparkling wine produced only in a specific region in France. Therefore, similar sparkling wines from other regions cannot be labeled as champagne.
- Trade secrets: Trade secrets are proprietary, confidential information that are owned by an entity. These can include formulas, practices and processes. They typically have a high value, as often an entire brand (such as Coca-Cola or KFC) is based on a secret formula. Trade secrets can be sold or licensed by the owner.
Avoiding intellectual property violations, intellectual property infringement, or even IP theft by using technology is a necessary step to take in this era of data breaches and cyberattacks. Encryption and employing a firm that specializes in intellectual property protection (as well as other types of sensitive information) is a mandatory step in helping your organization keep its priceless intellectual property assets secure.
How Intellectual Property Can Be Compromised
Similar to any other type of computer hack or data breach, theft of intellectual property can be a devastating blow to any organization. These IP theft attacks can come from any number of external sources, and for any number of reasons. Naturally, keeping your IP rights, valuable IP, and other data within your network, safe from outside threats, is paramount.
However, not all theft of intellectual property is through foreign agents or competitors; quite often, it’s an “inside job” – meaning somebody within the organization is responsible for the crime. Failure to follow IP protection best practices and established security standards can lead to vulnerabilities within the network, giving insiders, who may not be authorized to access your IP files. Having IP protection systems and safeguards in place will help block intruders from poking around your proprietary files.
Ensuring The Security of Your Intellectual Property
The absolute best way to secure your intellectual property against IP infringement, theft and compromise is by using products and services that give you total control over your assets. Your intellectual property and IP rights are only as secure as the security practices your organization employs. Knowing which digital assets need the highest degree of security against IP infringement and theft is important. Utilizing security tools that include encryption, limiting the users that can access the data and monitoring tools that monitor, track and report activity are not simply important, but an absolute must-have for intellectual property protection.
Protection through Encryption
Data encryption plays an important role in protecting your company’s intellectual property rights and design patents. In short, data encryption is a process that translates your data into another form, rendering it unreadable to those who don’t have the password (or decryption key) to access it. There are a number of different types (and security levels) of encryption available, and they all protect your data’s confidentiality.
The most common type of data encryption in use is Advanced Encryption Standard (AES), which is what the U.S. government uses. There are also multiple flavors of AES, but the military-grade standard is 256-bit encryption, meaning an extremely robust key is required to decrypt the data. So, even in the unlikely event there is a data breach and your IP files are compromised, the high-level encryption will assure you that strong level of encryption will render your information unreadable to unauthorized users.
Conducting Business Inside Virtual Data Rooms
While encrypting individual files is a viable way to ensure your IP doesn’t fall into the wrong hands, enterprise-scale businesses need more robust solutions. This is where virtual data rooms play a critical role in intellectual property law and IP infringement. A virtual data room (or VDR) is an online location, a place where companies store (and share) confidential information in a “workspace.” In today’s cloud-based, file sharing world, a virtual data room is a necessity.
When it comes to selecting a company to host a virtual data room for your organization, there are several features you should look for, including:
- Security: Needless to say, your trusted virtual data room partner must offer enterprise encryption, a necessity that will keep all of your data safe.
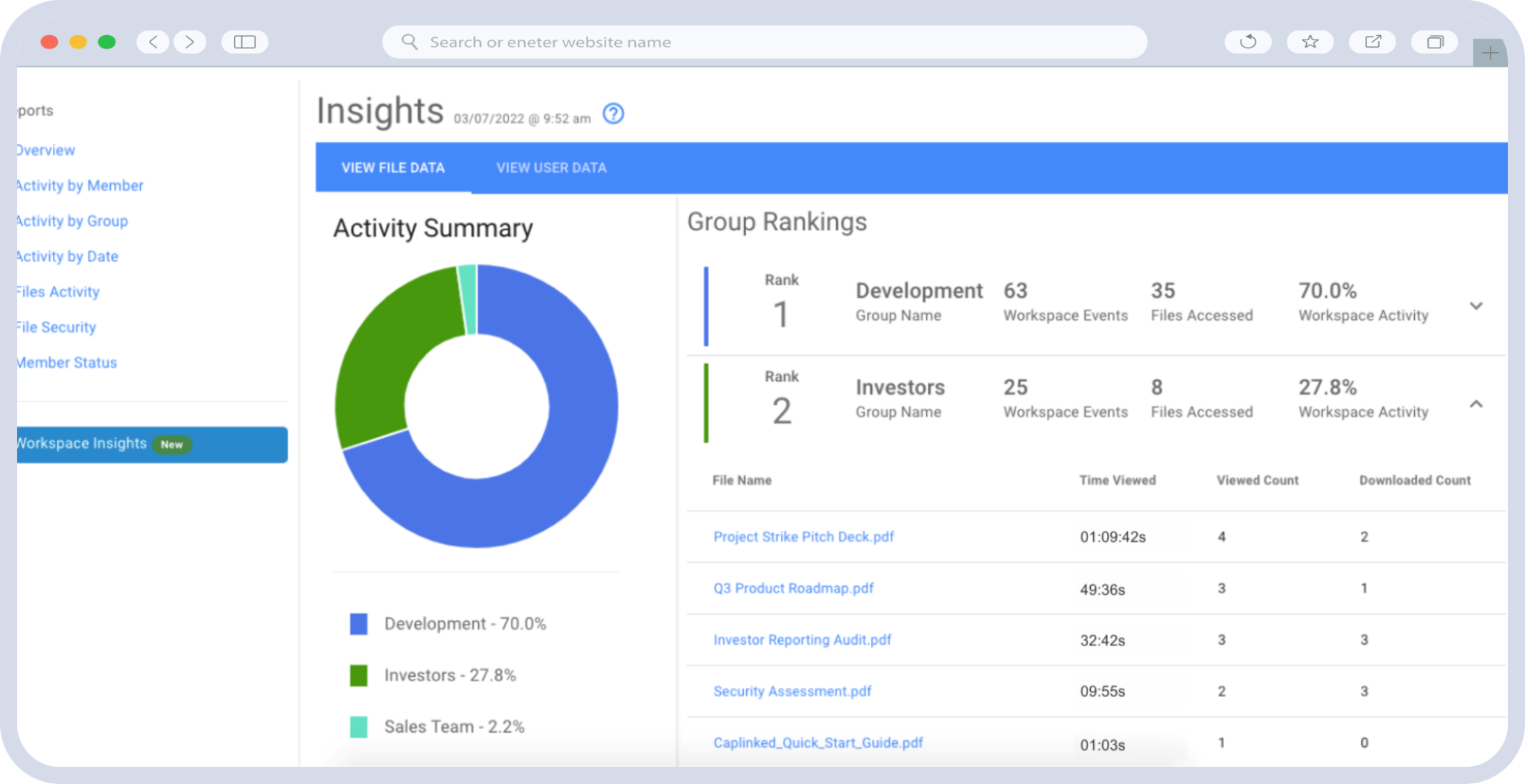
- User-friendliness: An interface that enables you to access all areas of your virtual data room, monitor all activity and view activity logs.
- Data management: The ability to seamlessly upload data from your workstation to your virtual data room, update and edit files that reside in your workspace.
In Closing
Intellectual property is one of your organization’s most valuable assets, and protection and confidentiality must be actively maintained. Finding a company to help you secure and manage your IP data is paramount — and not only one that provides world-class security, but also that has the tools to allow you to easily manage your data, and that has the reputation for uptime and 24/7/365 customer service.
CapLinked Virtual Data Rooms are trusted by over 250,000 professionals and nearly half of Fortune 1000 companies to keep their sensitive data and intellectual property secure. Interested in learning how? Request your free trial today.
Chris Capelle is a technology expert, writer and instructor. For over 25 years, he has worked in the publishing, advertising and consumer products industries.