Hardly a week goes by without a news story of another data breach or hack. Whether it’s mischief caused by professional hackers, amateurs causing chaos for fun, foreign nationals looking to breach government or military computers, or serious cybercriminals intent on holding a network hostage with ransomware, breaches happen frequently, and it’s a dangerous world out there as far as data privacy and data security is concerned. In 2021, cyberattacks cost somewhere in the neighborhood of $6 trillion, and that figure looks to do nothing but increase in subsequent years.
Table of Contents
ToggleThe Basics of Cybersecurity
Cybersecurity is the method that is used to protect any internet-connected devices from unauthorized users and criminal activity. It is a way to protect computers, networks and other connected devices from hackers, providing safeguards to the data and the users who access these networks and devices.
Cybersecurity depends on a lot of proactive work that is used to protect the confidentiality, availability and integrity of the data, sensitive information, and sensitive documents.
Function of a Virtual Data Room
A virtual data room (commonly abbreviated as VDR and sometimes referred to as a “deal room”) is a secure online repository used for document storage and distribution. This secure data room is commonly employed during the due diligence phase of mergers and acquisitions (M&As), when all parties involved in the transaction need to review, share, edit and disclose sensitive information that is relevant to the merger. In short, it’s a highly secure method to store documents that are required for a business transaction.
VDRs replace “physical” data rooms and offer a more secure way to track visitors. In addition, VDRs help expedite the transaction process by not requiring anyone’s physical presence, and they lower costs, as travel arrangements don’t have to be made, as the data can easily be accessed by anyone, no matter where they are based.
Can VDRs Be Hacked?
In general, VDRs are highly secure, with provisions made for virtual data protection. However, there are always threats that can compromise sensitive data and sensitive documents.
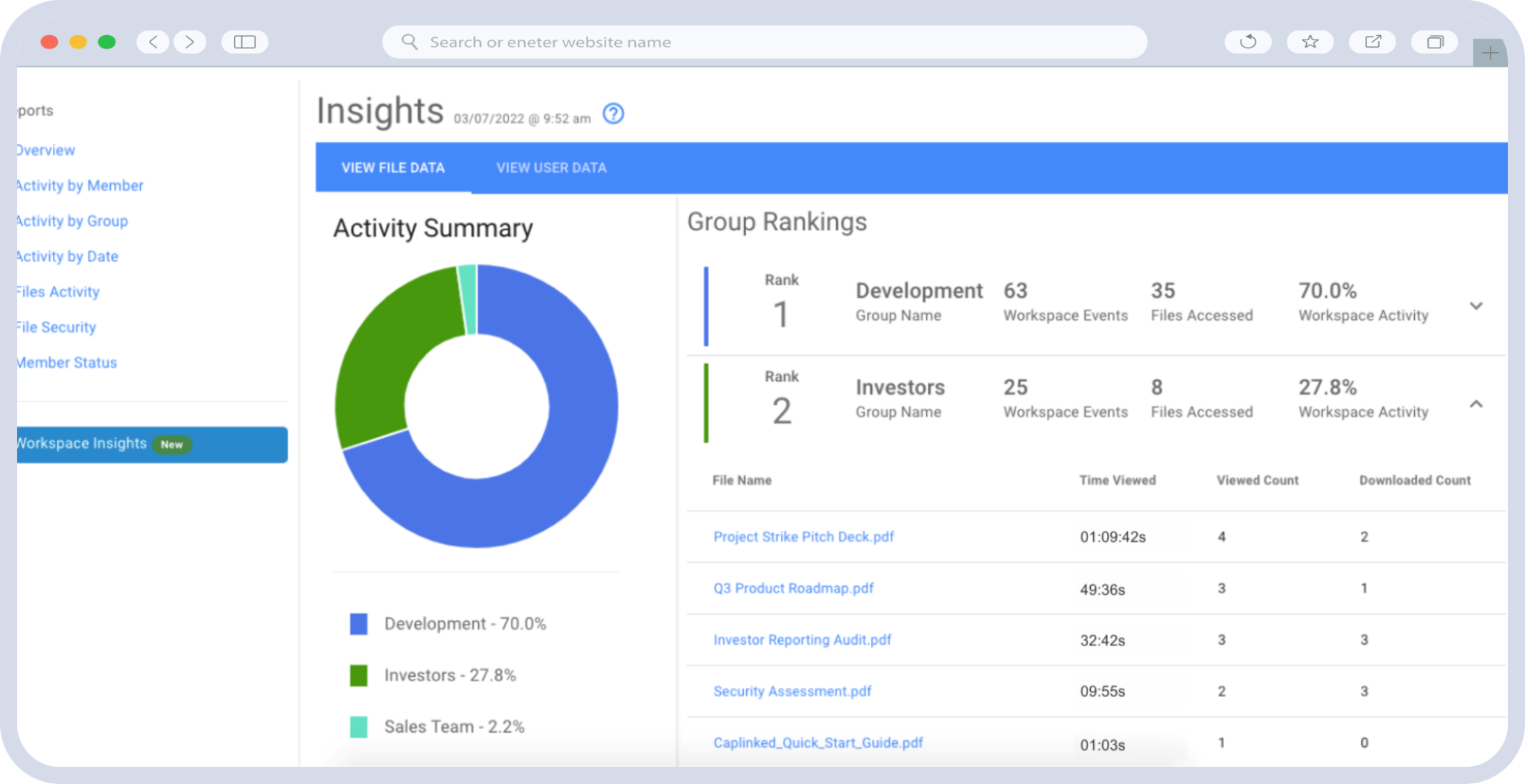
Many VDRs also feature built-in data loss prevention mechanisms. Administrators are able to see the logs on what data is accessed or edited by what party In a secure data room, permissions are set to allow only certain parties to access select documents. Also, admins control which groups are allowed to edit documents, and which groups are assigned read-only privileges. The high-level encryption system and the corresponding encryption keys are only accessed using a key management system. Finally, security options allow administrators to scan for malware, encrypt documents and use watermarks.
Best Practices for VDR Security
Needless to say, personal data privacy and the security of your digital data is paramount. Your data is likely to be your organization’s most valuable asset, and having it compromised can be a catastrophic event for your company.
There are some best practices for VDR personal data security, and they include the following:
- Use encryption: Encrypting your data allows authorized users (those with an encryption key) to view the documents seamlessly; unauthorized users won’t even be able to see the file structure.
- Configure permissions: Establishing group permissions is far simpler (and less time-consuming) than individual permissions. The good news is that you are able to specify certain levels of permissions — what files users are able to access and whether they have editing ability.
- Utilize DRM: Digital rights management (DRM) is software that allows admins to control and manage access to digital documentation. CapLinked’s FileProtect software limits user access based on several criteria, including authorized users/devices, IP addresses and specific hours to access the data.
- Watermark vital documents: A watermark is a “stamp” that indicates who has accessed, edited and/or downloaded the file. A digital watermark is added to the document, which includes identifiable information.
The Trusted CapLinked Solution
CapLinked’s virtual data rooms were designed from the outset with document security as a top priority. Its security features include multi-layer firewalls, a lockdown policy on insecure plugins, digital rights management, digital watermarks and two-factor authentication to ensure highly secure access.
CapLinked, an industry leader in the VDR space, can help keep your data secure in its virtual data rooms. To learn about CapLinked’s advanced security features, document collaboration controls, customizable permissions and more, contact CapLinked today to start your free trial.
Chris Capelle is a technology expert, writer and instructor. For over 25 years, he has worked in the publishing, advertising and consumer products industries.
Sources
Medium – Are Virtual Data Rooms Secure? [Data Room Security Guide]
Cybersecurity & Infrastructure Security Agency (CISA) – What is Cybersecurity?
National Initiative for Cybersecurity Careers and Studies (NICCS) – Cybersecurity Glossary